CS0-003 Practice Questions
CompTIA CyberSecurity Analyst CySA+ Certification Exam
Last Update 3 days ago
Total Questions : 486
Dive into our fully updated and stable CS0-003 practice test platform, featuring all the latest CompTIA CySA+ exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free CompTIA CySA+ practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CS0-003. Use this test to pinpoint which areas you need to focus your study on.
A corporation wants to implement an agent-based endpoint solution to help:
Flag various threats
Review vulnerability feeds
Aggregate data
Provide real-time metrics by using scripting languages
Which of the following tools should the corporation implement to reach this goal?
During a routine review of DNS logs, a security analyst observes that Host X has been making frequent DNS requests to domains with random alphanumeric strings, such as ajd8ekthj.xyz. IPS anomaly rules are blocking these domains. This behavior started shortly after a new software installation on the host. Which of the following should the analyst do first to determine whether Host X has been compromised?
An organization ' s email account was compromised by a bad actor. Given the following Information:
Which of the following is the length of time the team took to detect the threat?
An analyst is conducting monitoring against an authorized team that win perform adversarial techniques. The analyst interacts with the team twice per day to set the stage for the techniques to be used. Which of the following teams is the analyst a member of?
Due to reports of unauthorized activity that was occurring on the internal network, an analyst is performing a network discovery. The analyst runs an Nmap scan against a corporate network to evaluate which devices were operating in the environment. Given the following output:
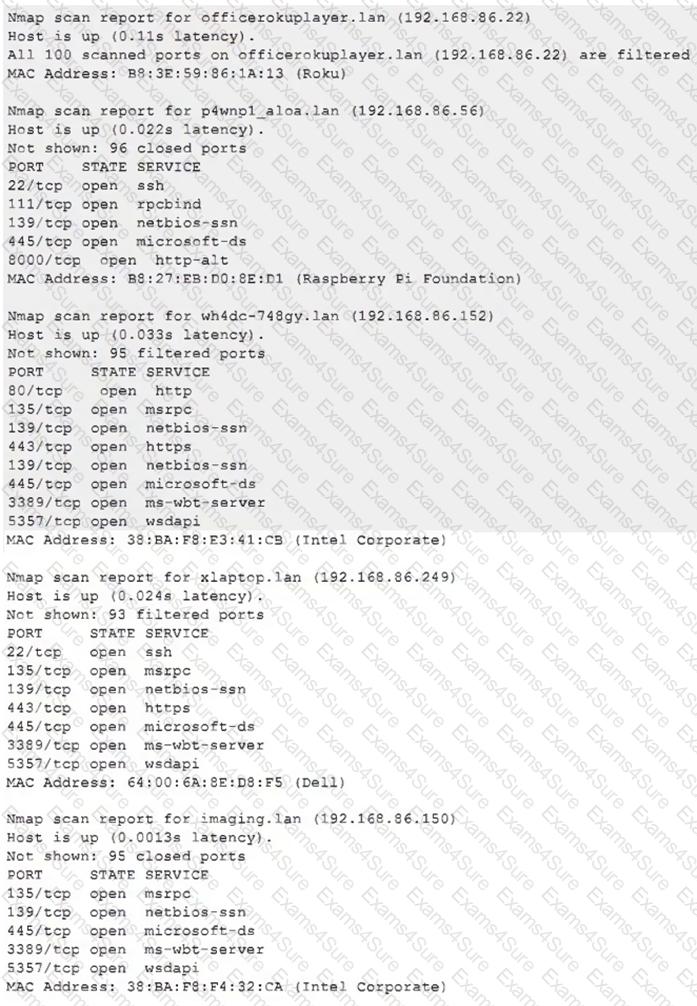
Which of the following choices should the analyst look at first?
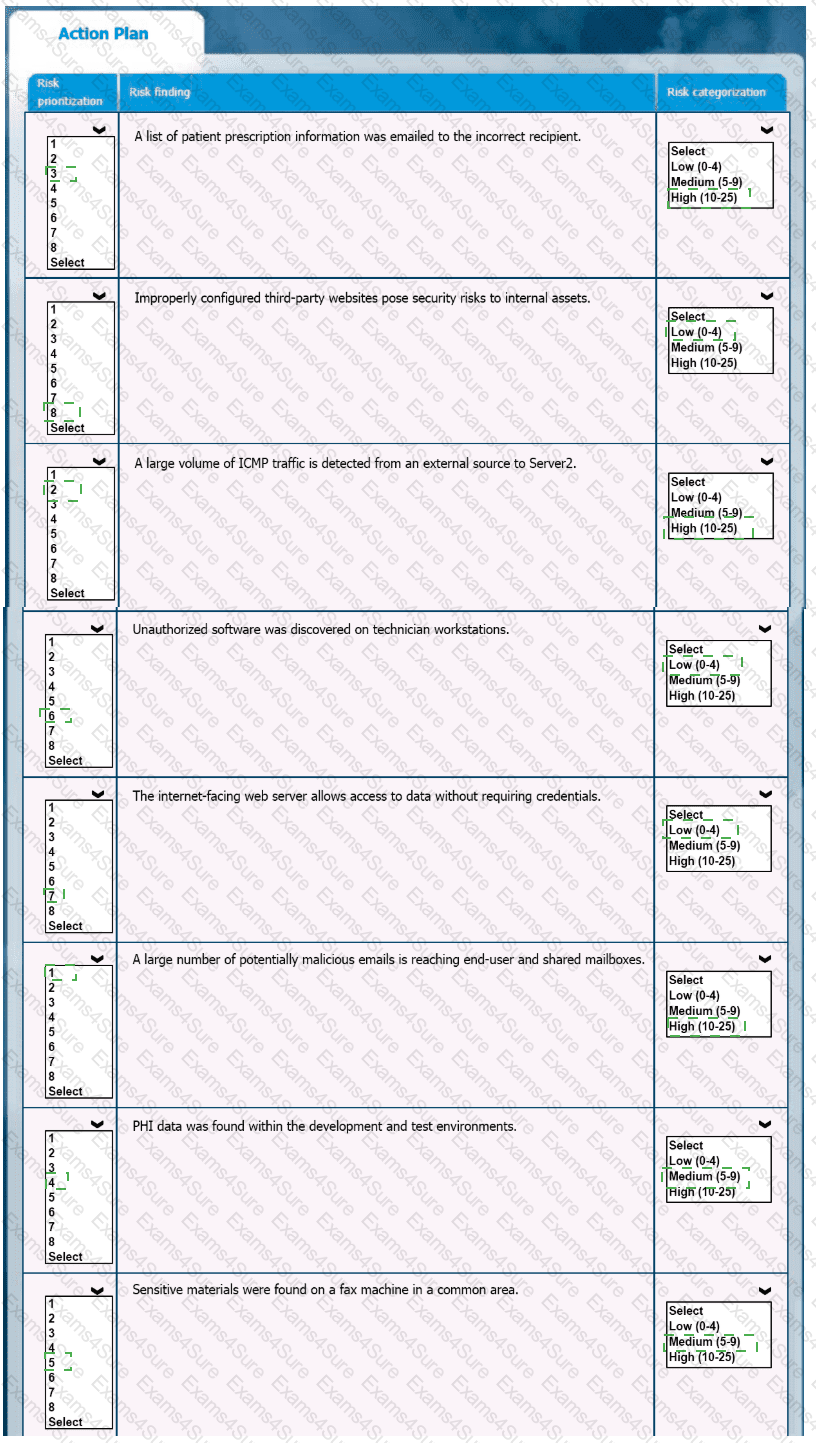
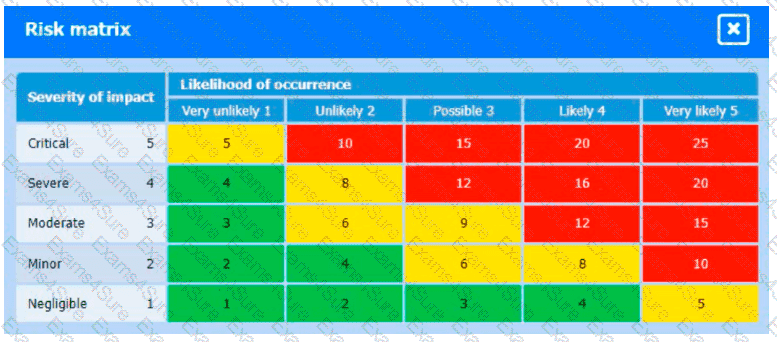
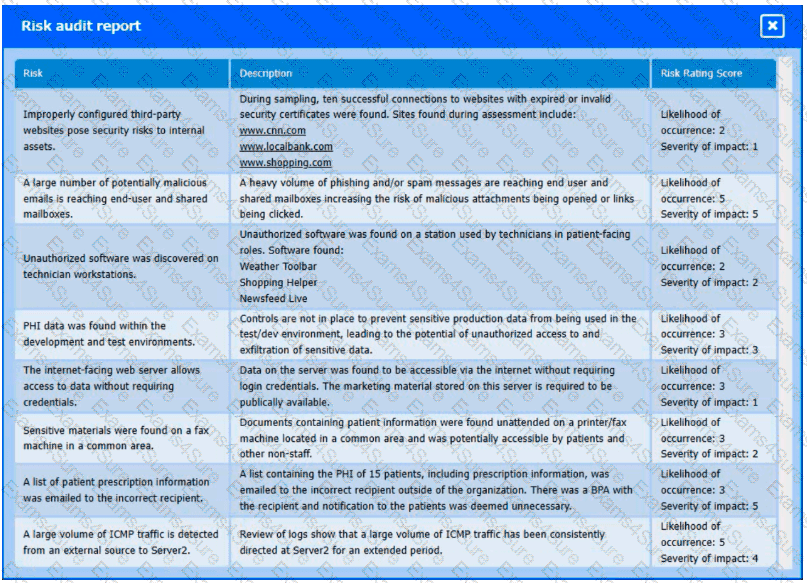
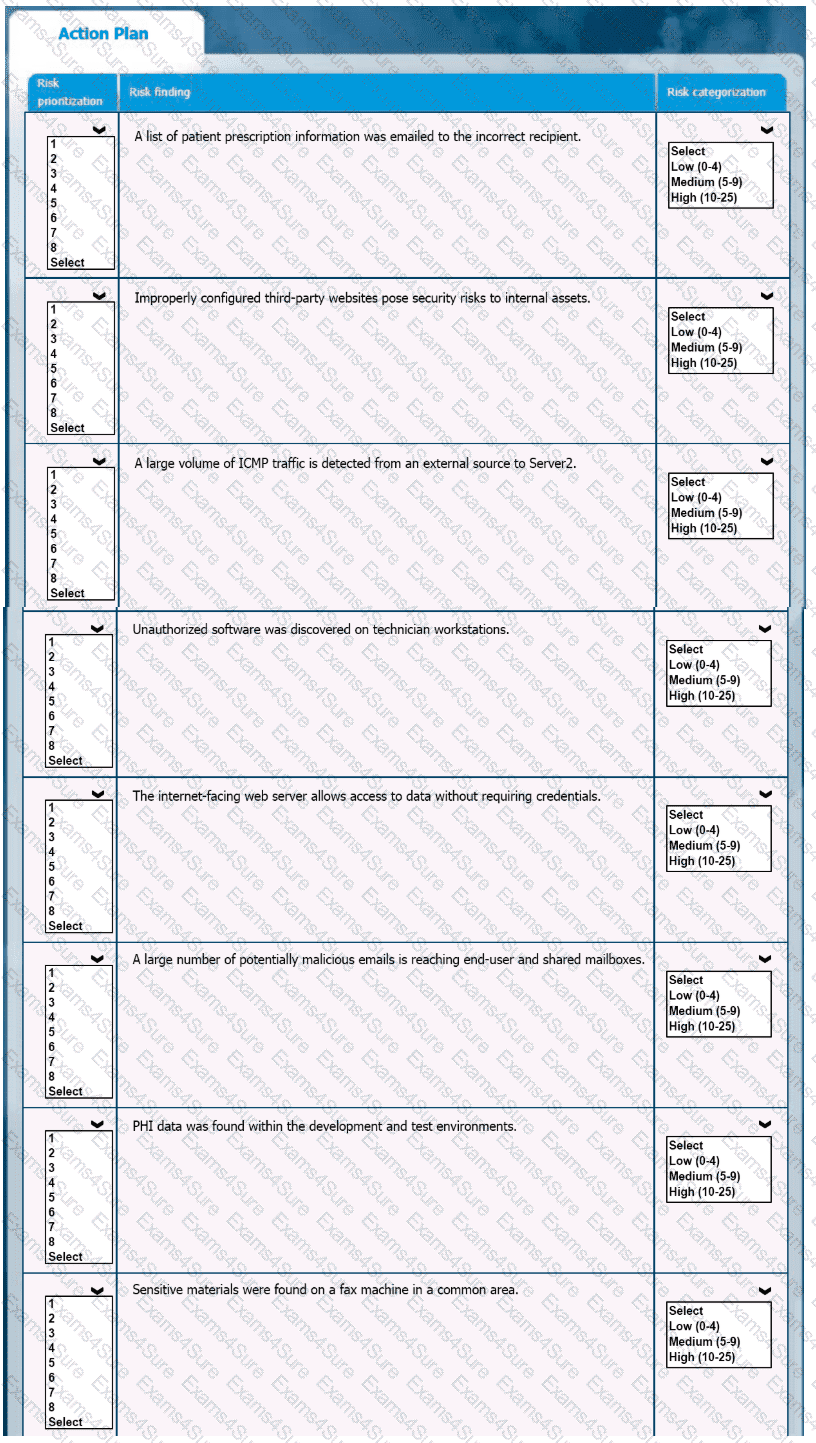
A healthcare organization must develop an action plan based on the findings from a risk assessment. The action plan must consist of risk categorization and prioritization.
INSTRUCTIONS
-
Click on the audit report and risk matrix to review their contents.
Assign a categorization to each risk and determine the order in which the findings must be prioritized for remediation according to the risk rating score.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
An incident response team is working with law enforcement to investigate an active web server compromise. The decision has been made to keep the server running and to implement compensating controls for a period of time. The web service must be accessible from the internet via the reverse proxy and must connect to a database server. Which of the following compensating controls will help contain the adversary while meeting the other requirements? (Select two).
A security operations center receives the following alerts related to an organization ' s cloud tenant:
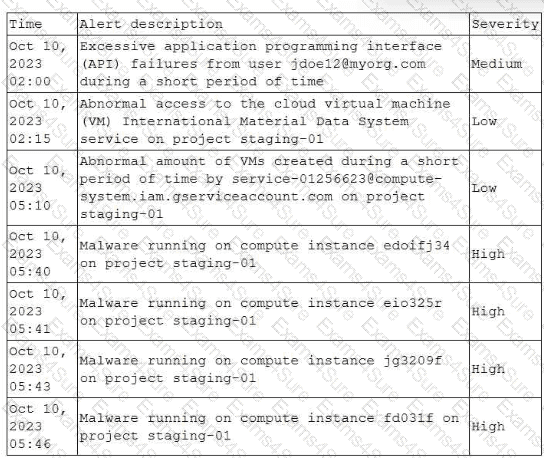
Which of the following should an analyst do first to identify the initial compromise?
Which Of the following techniques would be best to provide the necessary assurance for embedded software that drives centrifugal pumps at a power Plant?
A malicious actor has gained access to an internal network by means of social engineering. The actor does not want to lose access in order to continue the attack. Which of the following best describes the current stage of the Cyber Kill Chain that the threat actor is currently operating in?