CS0-003 Practice Questions
CompTIA CyberSecurity Analyst CySA+ Certification Exam
Last Update 3 days ago
Total Questions : 486
Dive into our fully updated and stable CS0-003 practice test platform, featuring all the latest CompTIA CySA+ exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free CompTIA CySA+ practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CS0-003. Use this test to pinpoint which areas you need to focus your study on.
An analyst views the following log entries:
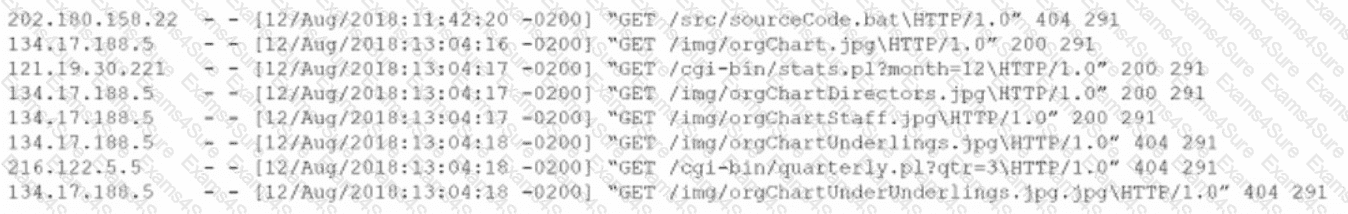
The organization has a partner vendor with hosts in the 216.122.5.x range. This partner vendor is required to have access to monthly reports and is the only external vendor with authorized access. The organization prioritizes incident investigation according to the following hierarchy: unauthorized data disclosure is more critical than denial of service attempts.
which are more important than ensuring vendor data access.
Based on the log files and the organization ' s priorities, which of the following hosts warrants additional investigation?
An analyst reviews the following web server log entries:
%2E%2E/%2E%2E/%2ES2E/%2E%2E/%2E%2E/%2E%2E/etc/passwd
No attacks or malicious attempts have been discovered. Which of the following most likely describes what took place?
A technician identifies a vulnerability on a server and applies a software patch. Which of the following should be the next step in the remediation process?
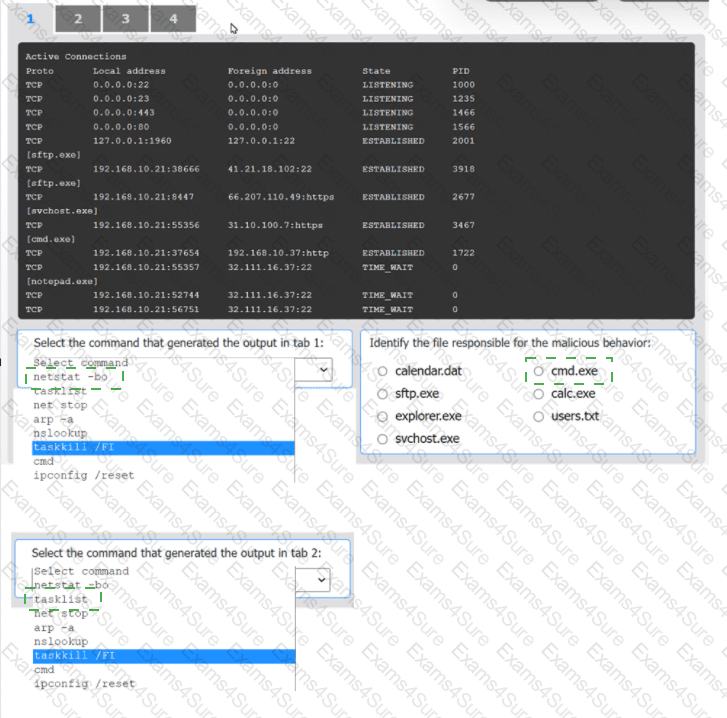
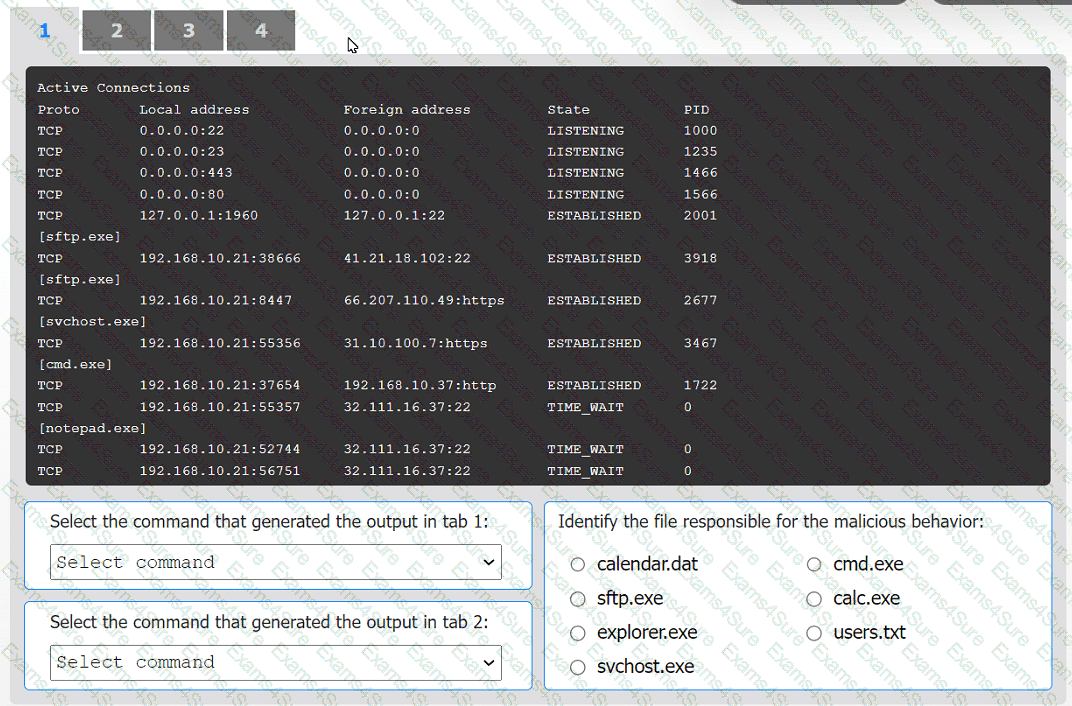
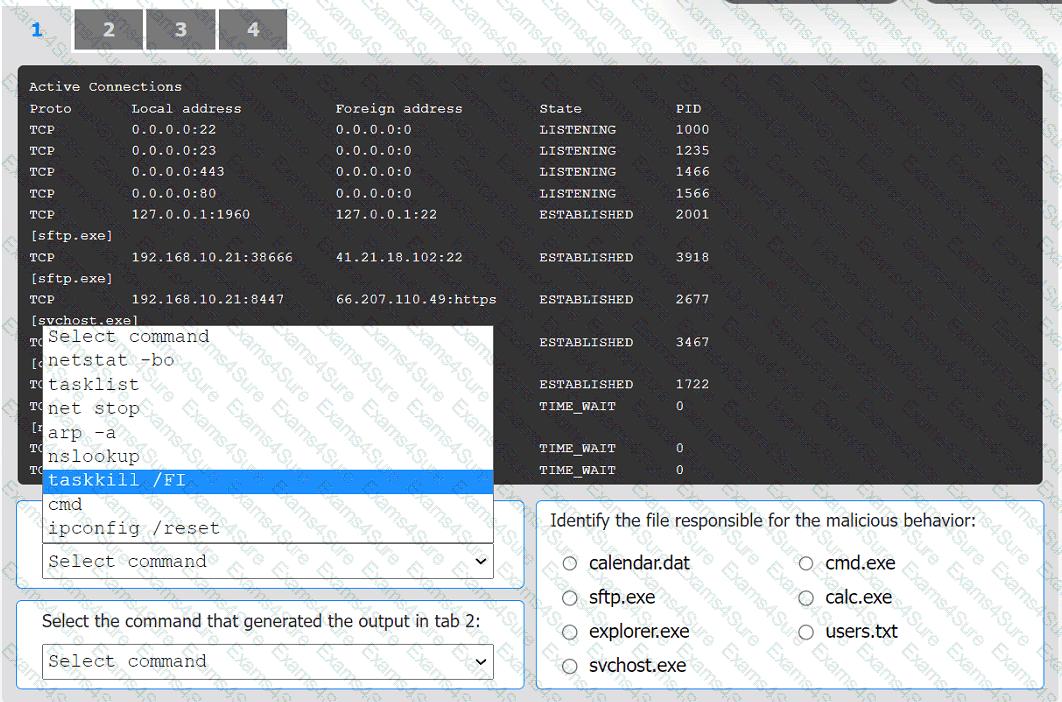
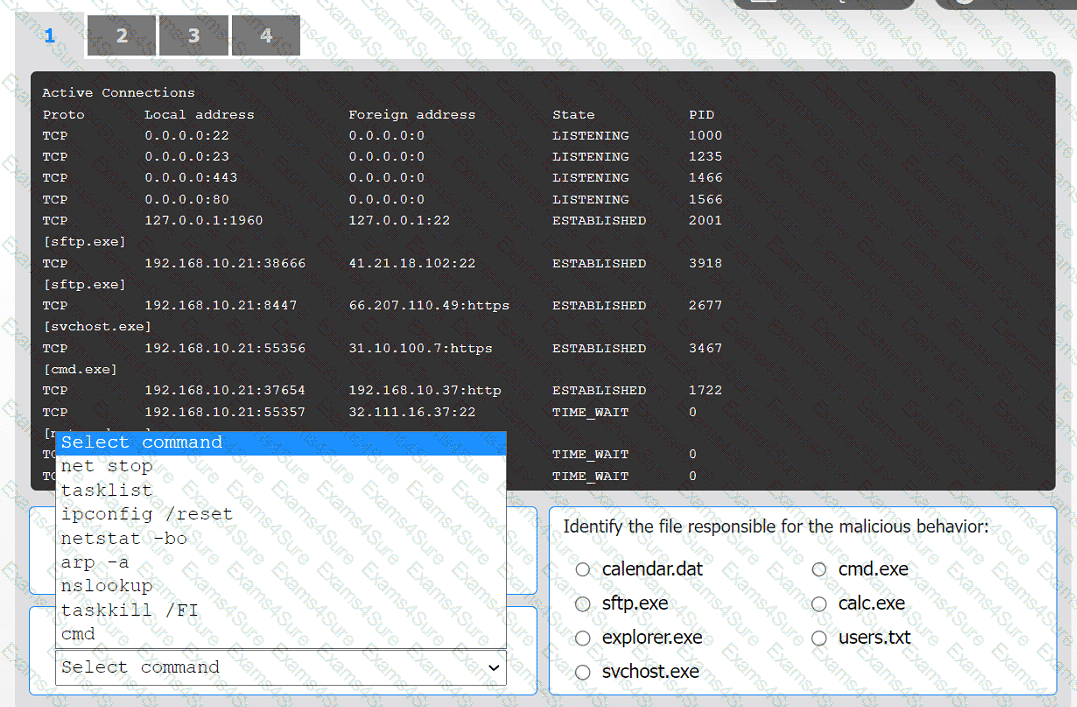
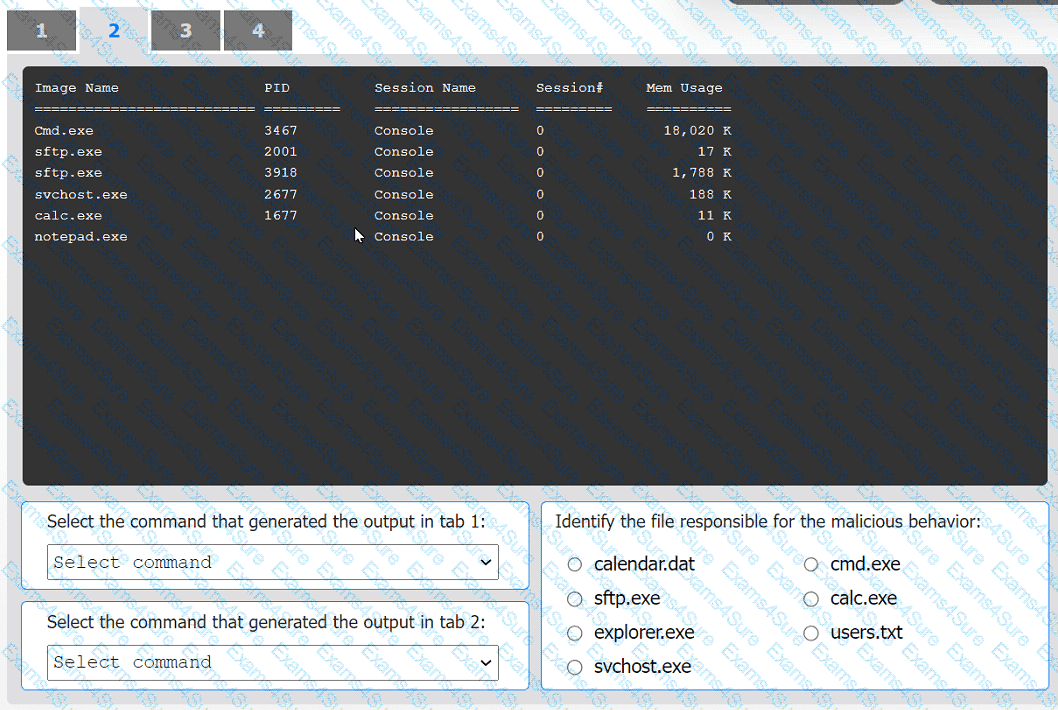
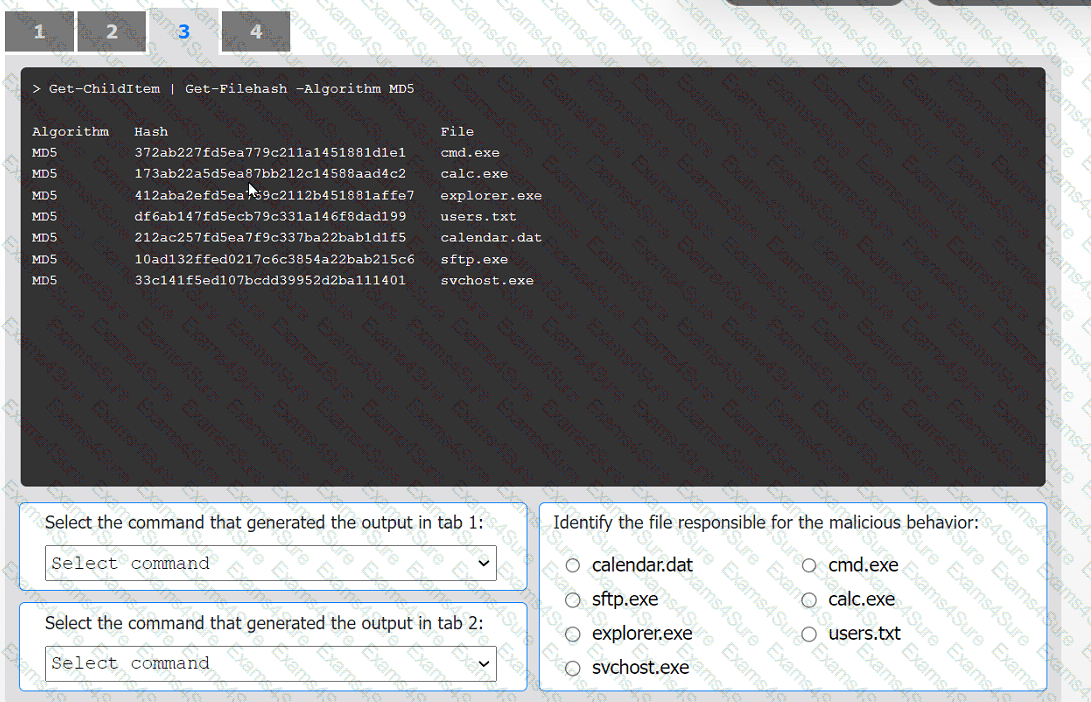
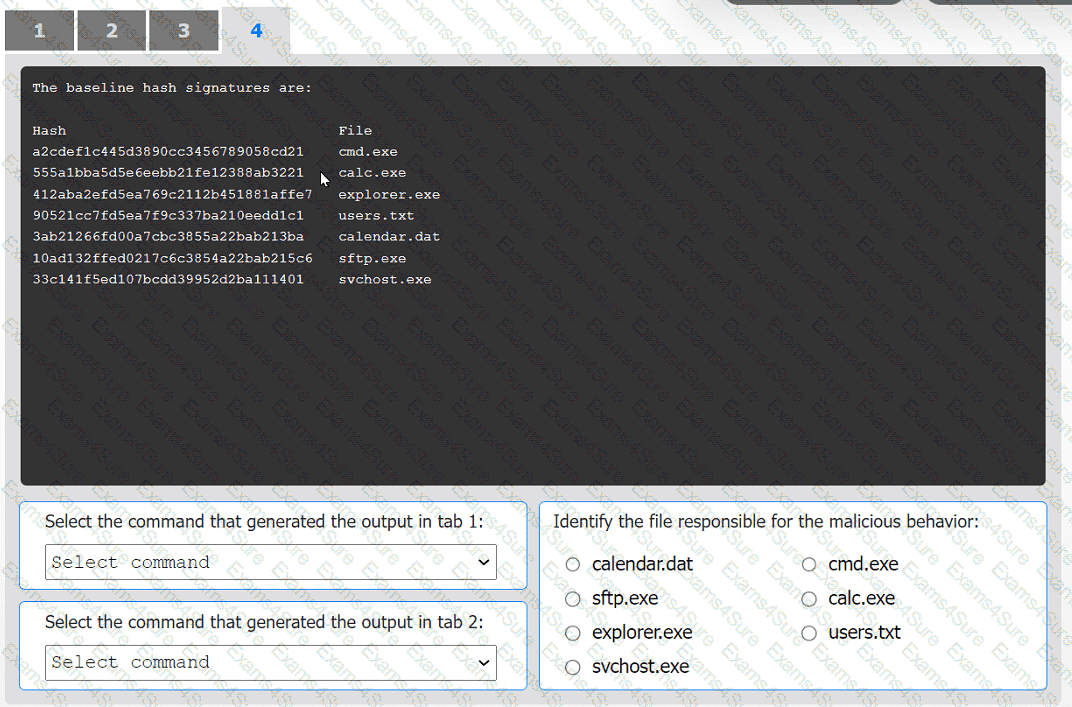
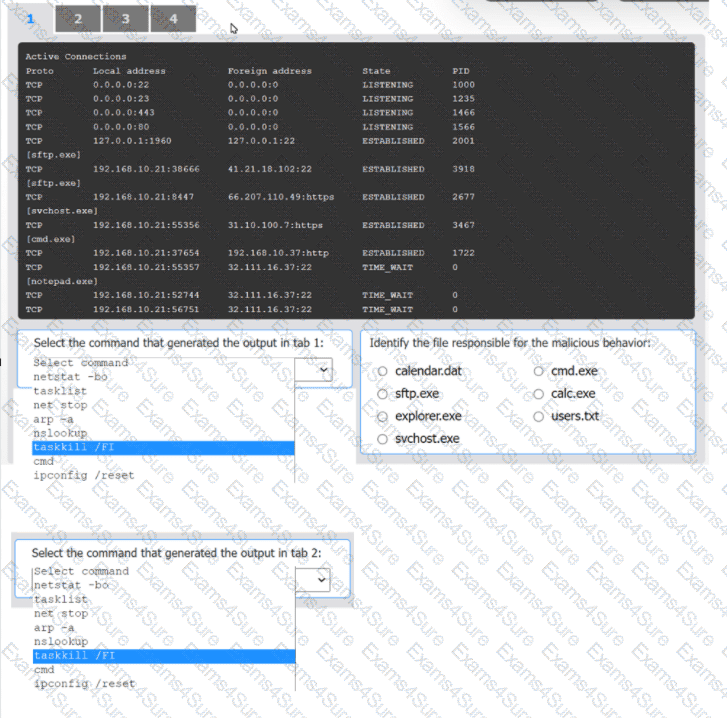
An organization has noticed large amounts of data are being sent out of its network. An
analyst is identifying the cause of the data exfiltration.
INSTRUCTIONS
Select the command that generated the output in tabs 1 and 2.
Review the output text in all tabs and identify the file responsible for the malicious
behavior.
If at any time you would like to bring back the initial state of the simulation, please click
the Reset All button.
The most recent vulnerability scan results show the following
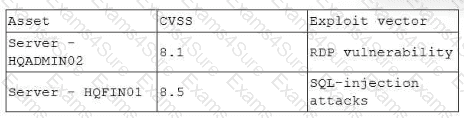
The vulnerability team learned the following from the asset owners:
• Server hqfinoi is a financial transaction database server used in the company ' s largest business unit.
• Server hqadmin02 is utilized by an end user with administrator privileges to several critical applications.
• No compensating controls exist for either issue.
Which of the following would the vulnerability team most likely do to determine remediation prioritization?
A company was able to reduce triage time by focusing on historical trend analysis. The business partnered with the security team to achieve a 50% reduction in phishing attempts year over year. Which of the following action plans led to this reduced triage time?
A systems administrator notices unfamiliar directory names on a production server. The administrator reviews the directory listings and files, and then concludes the server has been
compromised. Which of the following steps should the administrator take next?
An incident response team receives an alert to start an investigation of an internet outage. The outage is preventing all users in multiple locations from accessing external SaaS resources. The team determines the organization was impacted by a DDoS attack. Which of the following logs should the team review first?
Which of the following is the most likely reason for an organization to assign different internal departmental groups during the post-incident analysis and improvement process?
A security analyst wants to implement new monitoring controls in order to find abnormal account activity for traveling employees. Which of the following techniques would deliver the expected results?