
CS0-003 Practice Questions
CompTIA CyberSecurity Analyst CySA+ Certification Exam
Last Update 3 days ago
Total Questions : 486
Dive into our fully updated and stable CS0-003 practice test platform, featuring all the latest CompTIA CySA+ exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free CompTIA CySA+ practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CS0-003. Use this test to pinpoint which areas you need to focus your study on.
Which of the following would help to minimize human engagement and aid in process improvement in security operations?
After conducting a cybersecurity risk assessment for a new software request, a Chief Information Security Officer (CISO) decided the risk score would be too high. The CISO refused the software request. Which of the following risk management principles did the CISO select?
A security analyst needs to develop a solution to protect a high-value asset from an exploit like a recent zero-day attack. Which of the following best describes this risk management strategy?
A security analyst needs to identify the devices in a critical infrastructure network that handles an oil and gas pipeline. The network has devices connected over IPv4 using either HTTP or Modbus protocols running on the standard ports. Which of the following approaches should the analyst use to achieve the objective?
A cloud team received an alert that unauthorized resources were being auto-provisioned. After investigating, the team suspects that crypto mining is occurring. Which of the following indicators would
most likely lead the team to this conclusion?
.
A security analyst performs forensic analysis of a user’s computer. The analyst immediately orders the user to leave the computer powered on and not interact with it until further notice. Which of the following best describes the reason for the analyst’s orders?
An analyst has been asked to validate the potential risk of a new ransomware campaign that the Chief Financial Officer read about in the newspaper. The company is a manufacturer of a very small spring used in the newest fighter jet and is a critical piece of the supply chain for this aircraft. Which of the following would be the best threat intelligence source to learn about this new campaign?
An analyst is reviewing system logs while threat hunting:
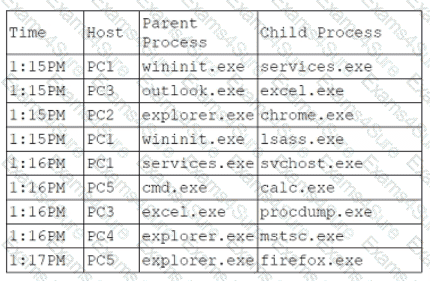
Which of the following hosts should be investigated first?
Which of the following is the first step that should be performed when establishing a disaster recovery plan?
Two employees in the finance department installed a freeware application that contained embedded malware. The network is robustly segmented based on areas of responsibility. These computers had critical sensitive information stored locally that needs to be recovered. The department manager advised all department employees to turn off their computers until the security team could be contacted about the issue. Which of the following is the first step the incident response staff members should take when they arrive?



