SC-200 Practice Questions
Microsoft Security Operations Analyst
Last Update 2 days ago
Total Questions : 388
Dive into our fully updated and stable SC-200 practice test platform, featuring all the latest Microsoft Certified: Security Operations Analyst Associate exam questions added this week. Our preparation tool is more than just a Microsoft study aid; it's a strategic advantage.
Our free Microsoft Certified: Security Operations Analyst Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about SC-200. Use this test to pinpoint which areas you need to focus your study on.
You have multiple Azure subscriptions that contain multiple Microsoft Sentinel workspaces.
You are creating a Microsoft Sentinel workbook that will include references to the AzureActivity table.
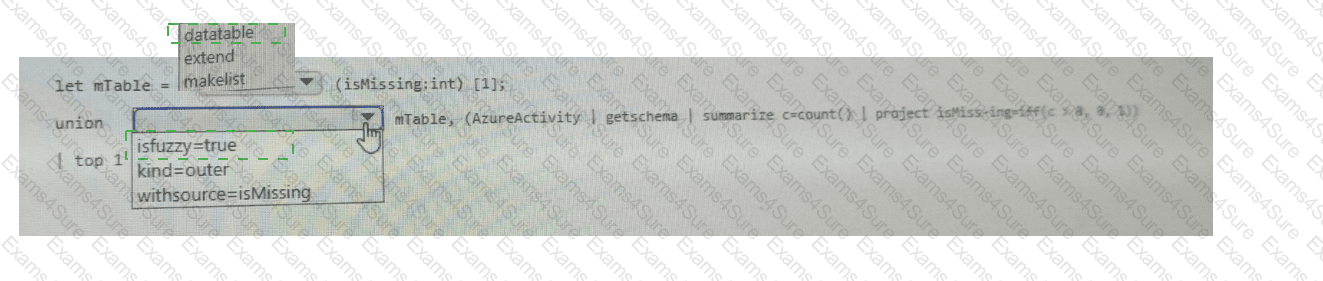
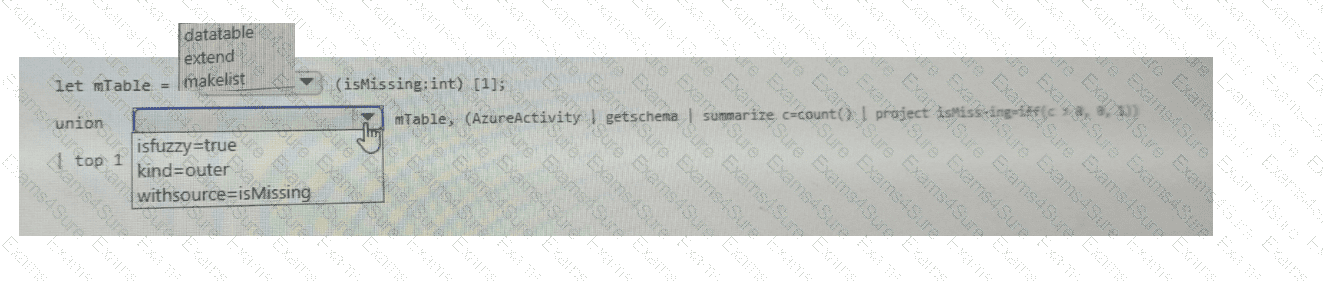
You need to create a KQL query that will perform the following actions:
. Check whether the AzureActivity table exists in each workspace.
. If the table exists, return a single row that has the isMissing column set to 0.
. If the table does NOT exist, return a single row that has the isMissing column set to 1.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that uses Microsoft Defender for Servers Plan 1 and contains a server named Server1.
You enable agentless scanning.
You need to prevent Server1 from being scanned. The solution must minimize administrative effort.
What should you do?
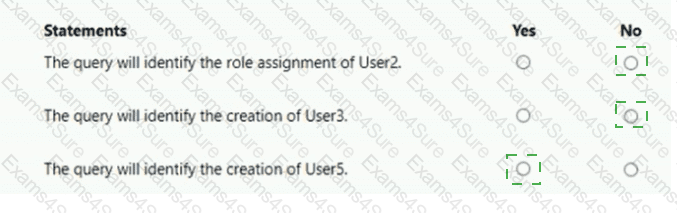
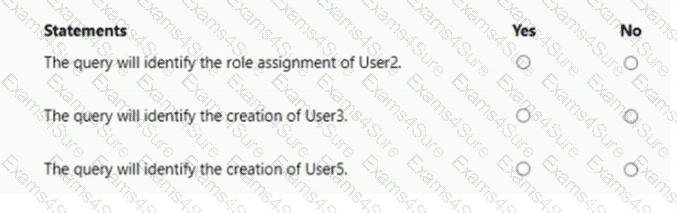
You have a Microsoft 365 E5 subscription that contains two users named User1 and User2. You have the hunting query shown in the following exhibit.
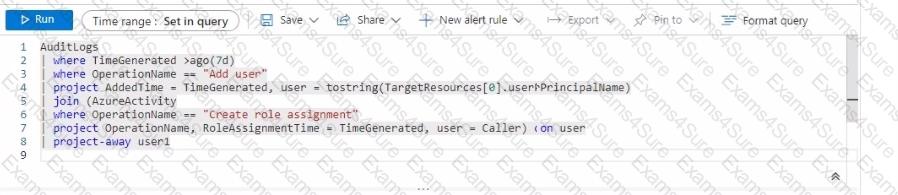
The users perform the following actions:
• User1 assigns User2 the Global Administrator role.
• User1 creates a new user named User3 and assigns the user a Microsoft Teams license.
• User2 creates a new user named User4 and assigns the user the Security Reader role.
• User2 creates a new user named User5 and assigns the user the Security Operator role.
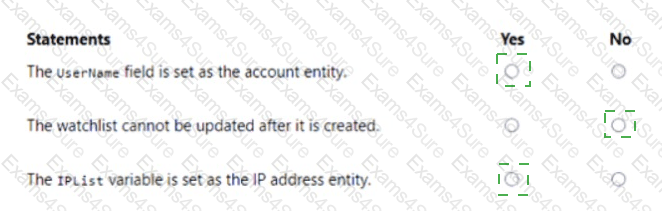
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
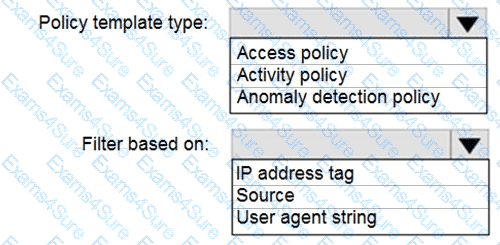
You purchase a Microsoft 365 subscription.
You plan to configure Microsoft Cloud App Security.
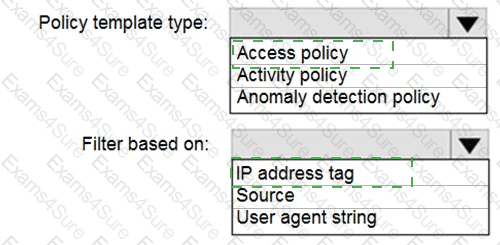
You need to create a custom template-based policy that detects connections to Microsoft 365 apps that originate from a botnet network.
What should you use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Your company deploys the following services:
Microsoft Defender for Identity
Microsoft Defender for Endpoint
Microsoft Defender for Office 365
You need to provide a security analyst with the ability to use the Microsoft 365 security center. The analyst must be able to approve and reject pending actions generated by Microsoft Defender for Endpoint. The solution must use the principle of least privilege.
Which two roles should assign to the analyst? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point .
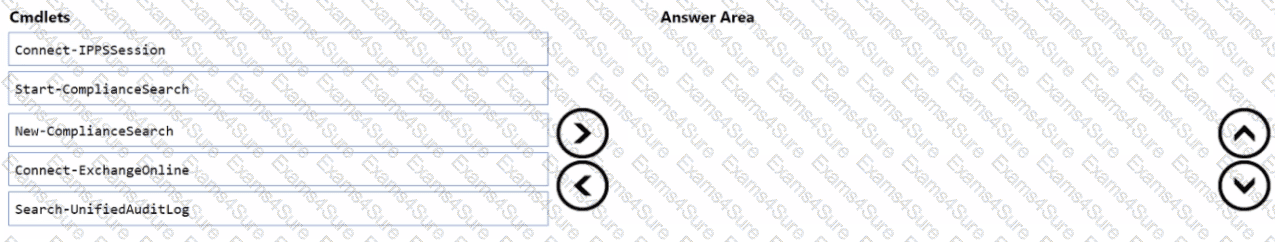
You have a Microsoft 365 E5 subscription that uses Microsoft Exchange Online.
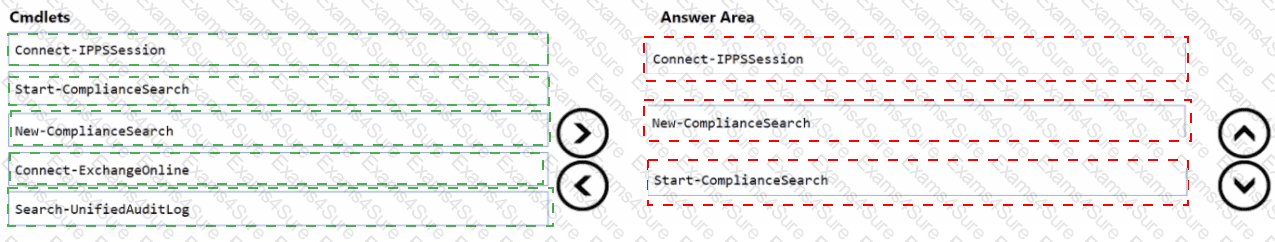
You need to identify phishing email messages.
Which three cmdlets should you run in sequence? To answer, move the appropriate cmdlets from the list of cmdlets to the answer area and arrange them in the correct order.
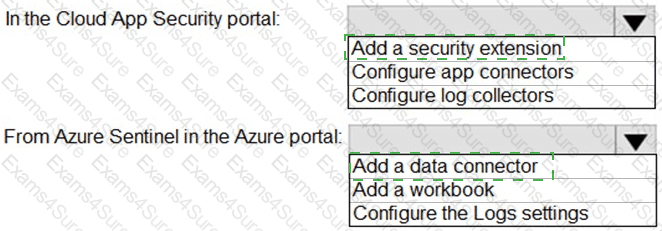
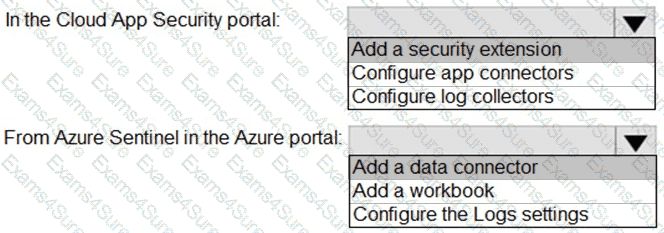
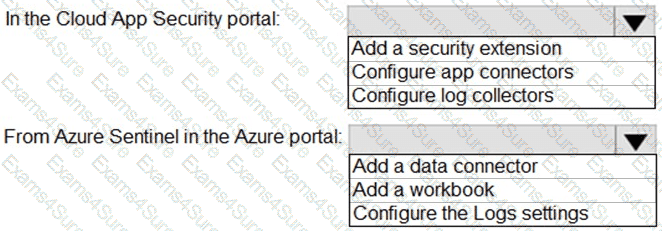
You need to configure the Azure Sentinel integration to meet the Azure Senti nel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to modify the anomaly detection policy settings to meet the Microsoft Defender for Cloud Apps requirements and resolve the reported problem.
Which policy should you modify?
You have a Microsoft 365 E5 subscription that contains 100 Linux devices. The devices are onboarded to Microsoft Defender 365. You need to initiate the collection of investigation packages from the devices by using the Microsoft 365 Defender portal. Which response action should you use?