SC-200 Practice Questions
Microsoft Security Operations Analyst
Last Update 2 days ago
Total Questions : 388
Dive into our fully updated and stable SC-200 practice test platform, featuring all the latest Microsoft Certified: Security Operations Analyst Associate exam questions added this week. Our preparation tool is more than just a Microsoft study aid; it's a strategic advantage.
Our free Microsoft Certified: Security Operations Analyst Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about SC-200. Use this test to pinpoint which areas you need to focus your study on.
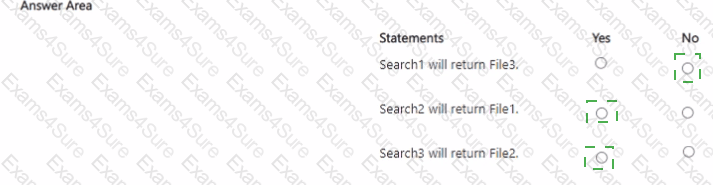
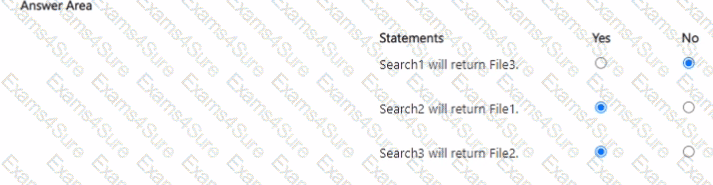
You have a Microsoft 365 subscription that uses Microsoft Purview and contains a Microsoft SharePoint Online site named Site1. Site1 contains the files shown in the following table.
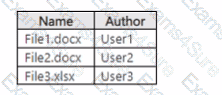
From Microsoft Purview, you create the content search queries shown in the following table.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE; Each correct selection is worth one point.
Your on-premises network contains two Active Directory Domain Services (AD DS) domains named contoso.com and fabrikam.com. Contoso.com contains a group named Group1. Fabrikam.com contains a group named Group2.
You have a Microsoft Sentinel workspace named WS1 that contains a scheduled query rule named Rule1. Rule1 generates alerts in response to anomalous AD DS security events. Each alert creates an incident.
You need to implement an incident triage solution that meets the following requirements:
· Security incidents from contoso.com must be assigned to Group1.
· Security incidents from fabrikam.com must be assigned to Group2.
· Administrative effort must be minimized.
What should you include in the solution?
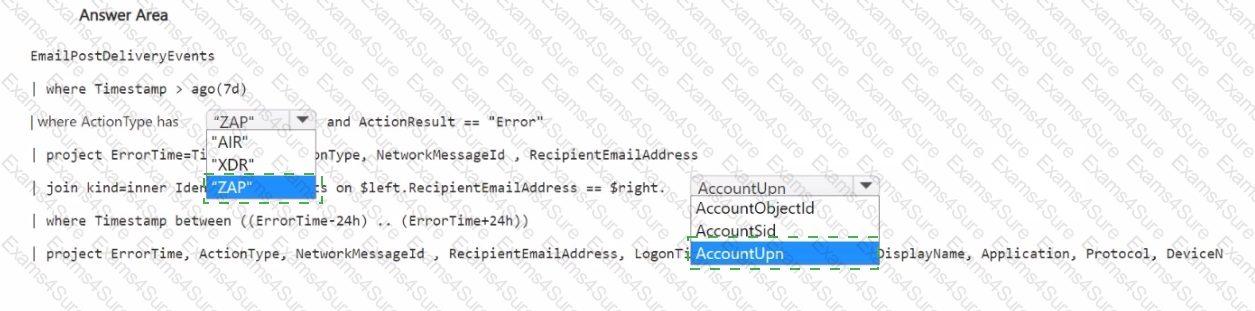
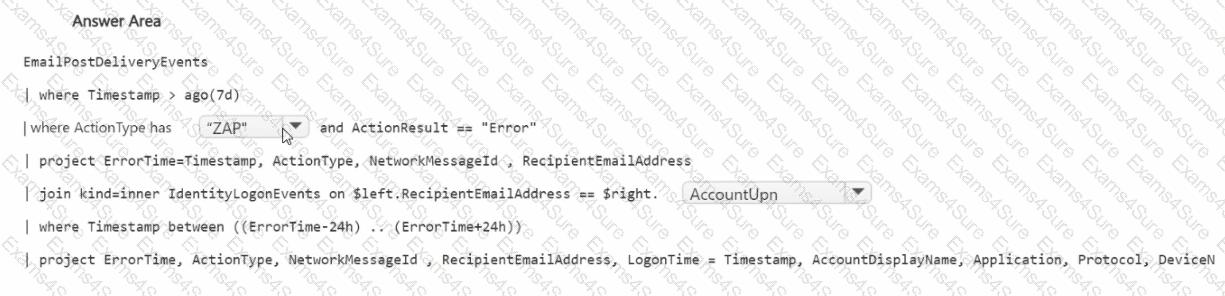
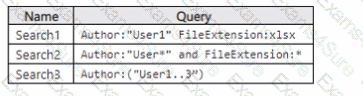
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Office 365.
You need to build a hunting query that will list events involving potentially malicious emails that were detected but NOT removed successfully from mailboxes after delivery. The solution must ensure that the events are correlated with the sign-in events of the email recipients.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
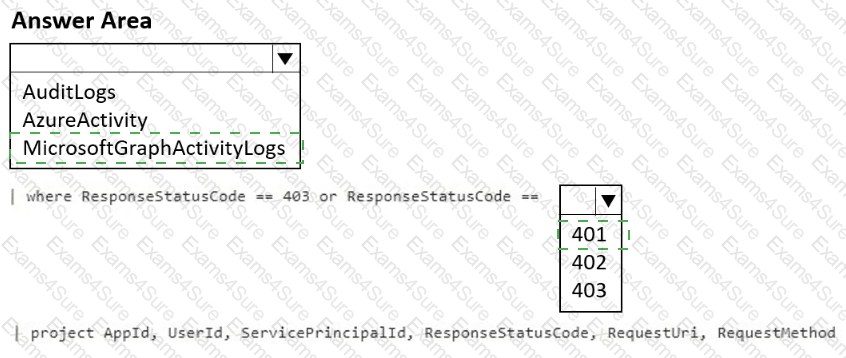
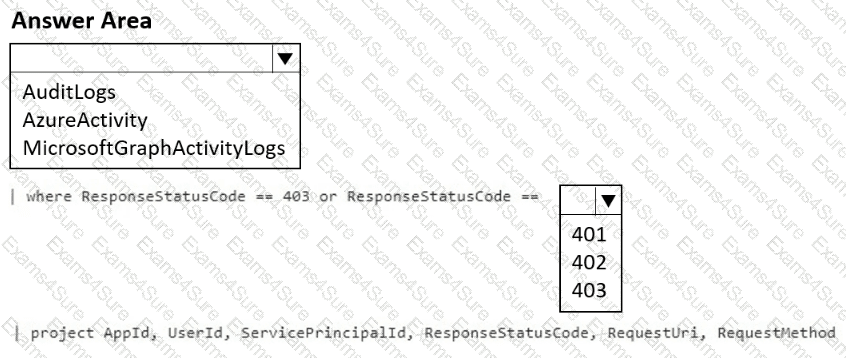
You have an Azure subscription that contains a Log Analytics workspace named Workspace1.
You configure Azure activity logs and Microsoft Entra ID logs to be forwarded to Workspace1.
You need to query Workspace1 to identify all the requests that failed due to insufficient authorization.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
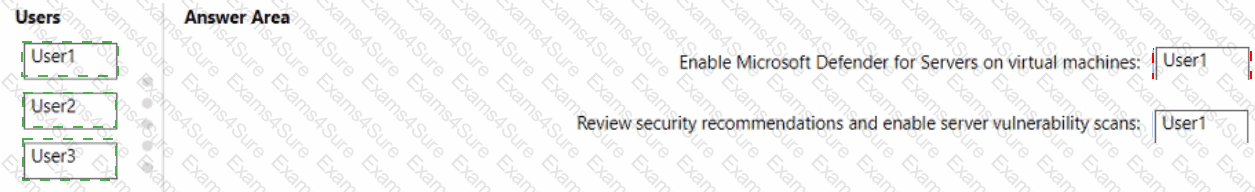
You have an Azure subscription that contains the users shown in the following table.
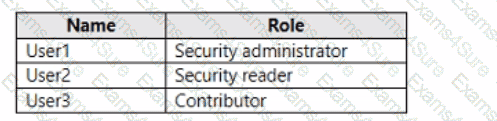
You need to delegate the following tasks:
• Enable Microsoft Defender for Servers on virtual machines.
• Review security recommendations and enable server vulnerability scans.
The solution must use the principle of least privilege.
Which user should perform each task? To answer, drag the appropriate users to the correct tasks. Each user may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
You have 1,000 on-premises Windows 11 Pro devices that are onboarded to Microsoft Defender for Endpoint. You have a Microsoft 365 subscription that uses Microsoft Defender XDR. You identify that an attacker performed the following actions on a device:
• Modified the file system path of a registry-based antivirus exclusion
• Downloaded a malicious file to the file system path
You initiate a live response session on the device. You need to undo the registry change. Which command should you run?
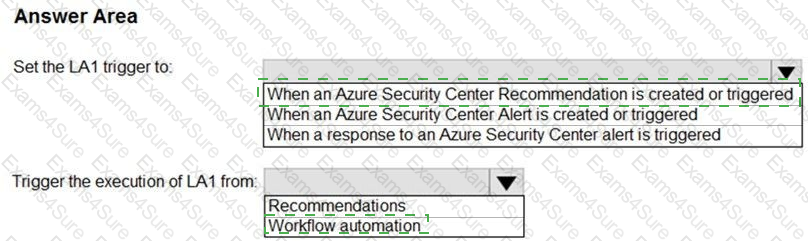
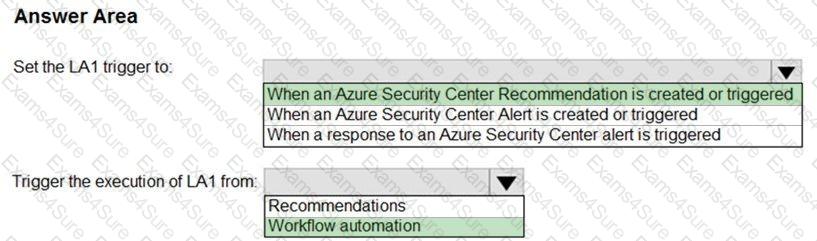
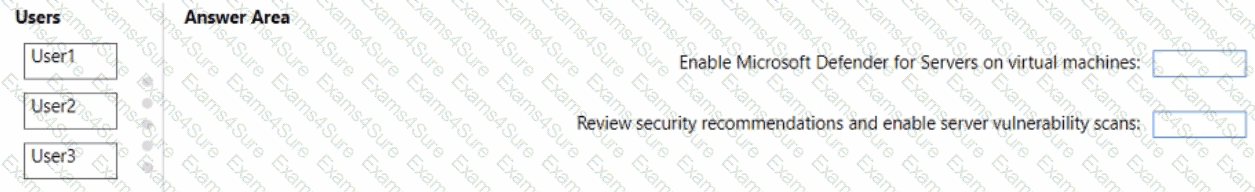
You have an Azure subscrip tion that has Azure Defender enabled for all supported resource types.
You create an Azure logic app named LA1.
You plan to use LA1 to automatically remediate security risks detected in Azure Security Center.
View the window
You need to test LA1 in Security Center.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that contains a Microsoft Sentinel workspace. The workspace contains a Microsoft Defender for Cloud data connector. You need to customize which details will be included when an alert is created for a specific event. What should you do?
You need to remediate ac tive attacks to meet the technical requirements.
What should you include in the solution?
You need to recommend a solution to meet the technical requirements for the Azure virtual machines. What should you include in the recommendation?