
CEH-001 Practice Questions
Certified Ethical Hacker (CEH)
Last Update 3 days ago
Total Questions : 878
Dive into our fully updated and stable CEH-001 practice test platform, featuring all the latest Certified Ethical Hacker CEH exam questions added this week. Our preparation tool is more than just a GAQM study aid; it's a strategic advantage.
Our free Certified Ethical Hacker CEH practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CEH-001. Use this test to pinpoint which areas you need to focus your study on.
Your boss Tess King is attempting to modify the parameters of a Web-based application in order to alter the SQL statements that are parsed to retrieve data from the database. What would you call such an attack?
The programmers on your team are analyzing the free, open source software being used to run FTP services on a server. They notice that there is an excessive number of fgets() and gets() on the source code. These C++ functions do not check bounds.
What kind of attack is this program susceptible to?
Why do you need to capture five to ten million packets in order to crack WEP with AirSnort?
Bryan notices the error on the web page and asks Liza to enter liza' or '1'='1 in the email field. They are greeted with a message "Your login information has been mailed to johndoe@gmail.com". What do you think has occurred?
Which of the following wireless technologies can be detected by NetStumbler? (Select all that apply)
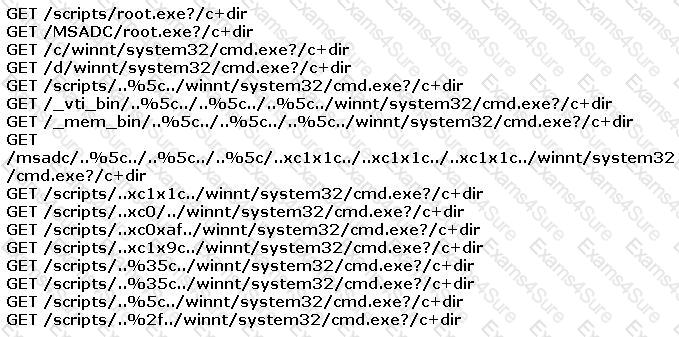
You find the following entries in your web log. Each shows attempted access to either root.exe or cmd.exe.
What caused this?
Derek has stumbled upon a wireless network and wants to assess its security. However, he does not find enough traffic for a good capture. He intends to use AirSnort on the captured traffic to crack the WEP key and does not know the IP address range or the AP. How can he generate traffic on the network so that he can capture enough packets to crack the WEP key?
After studying the following log entries, how many user IDs can you identify that the attacker has tampered with?
1. mkdir -p /etc/X11/applnk/Internet/.etc
2. mkdir -p /etc/X11/applnk/Internet/.etcpasswd
3. touch -acmr /etc/passwd /etc/X11/applnk/Internet/.etcpasswd
4. touch -acmr /etc /etc/X11/applnk/Internet/.etc
5. passwd nobody -d
6. /usr/sbin/adduser dns -d/bin -u 0 -g 0 -s/bin/bash
7. passwd dns -d
8. touch -acmr /etc/X11/applnk/Internet/.etcpasswd /etc/passwd
9. touch -acmr /etc/X11/applnk/Internet/.etc /etc
Which of the following cryptography attack methods is usually performed without the use of a computer?



