
CEH-001 Practice Questions
Certified Ethical Hacker (CEH)
Last Update 2 days ago
Total Questions : 878
Dive into our fully updated and stable CEH-001 practice test platform, featuring all the latest Certified Ethical Hacker CEH exam questions added this week. Our preparation tool is more than just a GAQM study aid; it's a strategic advantage.
Our free Certified Ethical Hacker CEH practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CEH-001. Use this test to pinpoint which areas you need to focus your study on.
Here is the ASCII Sheet.
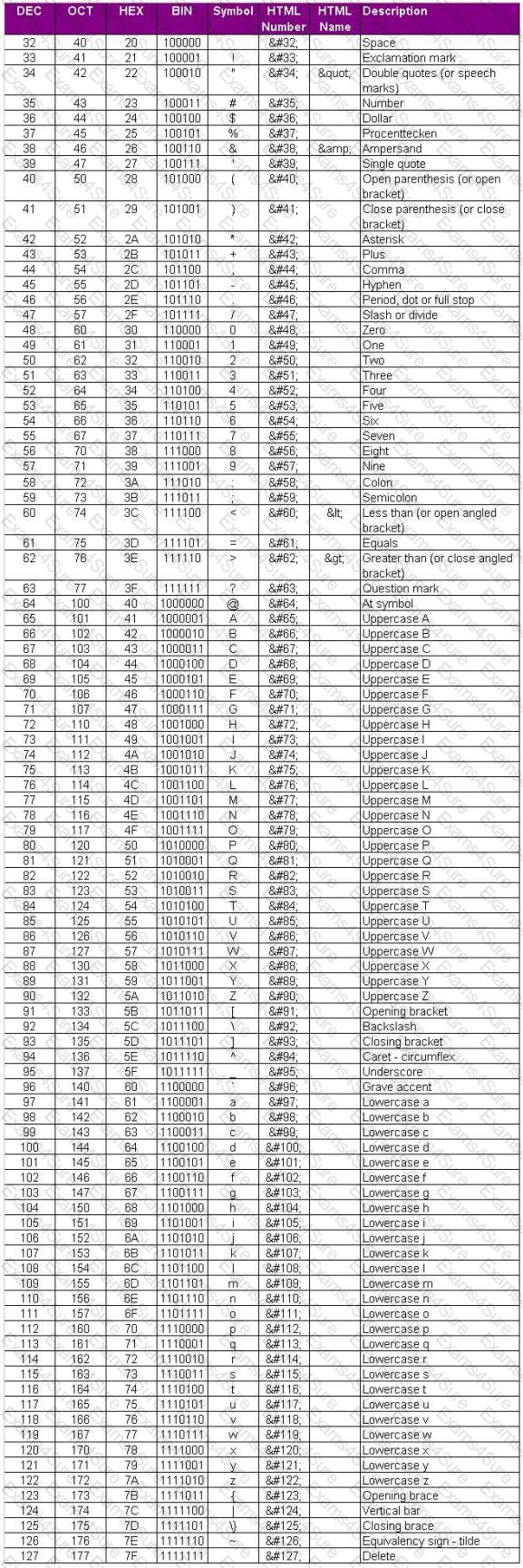
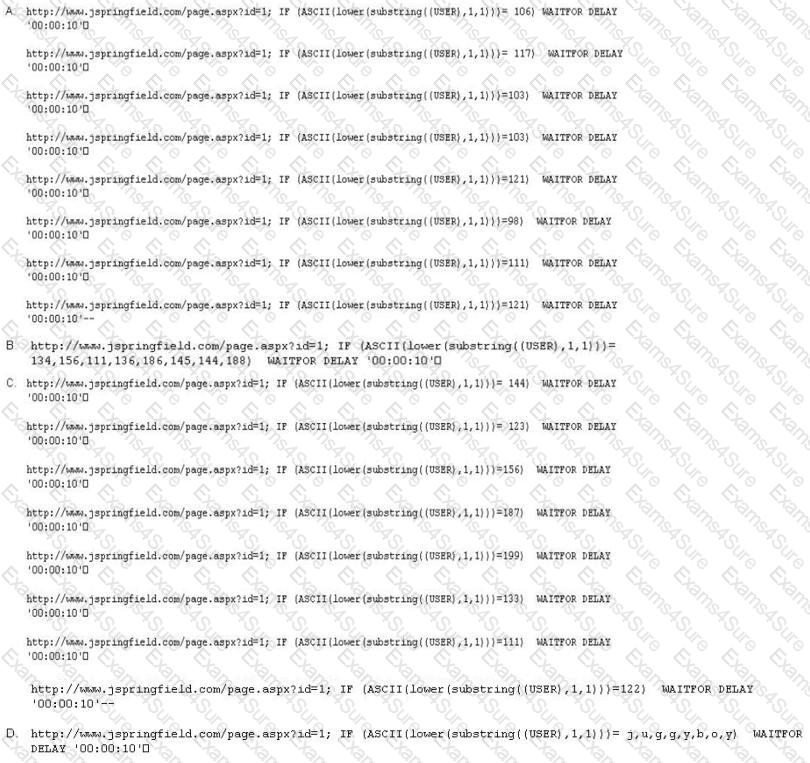
You want to guess the DBO username juggyboy (8 characters) using Blind SQL Injection technique.
What is the correct syntax?
Which of the following can take an arbitrary length of input and produce a message digest output of 160 bit?
You generate MD5 128-bit hash on all files and folders on your computer to keep a baseline check for security reasons?
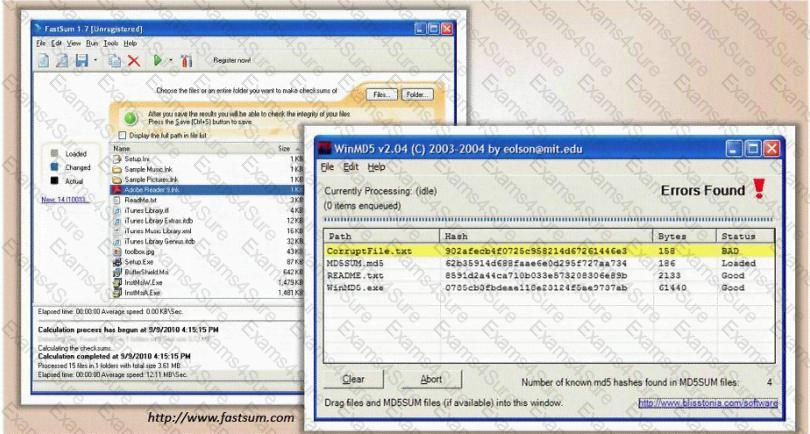
What is the length of the MD5 hash?
A company has made the decision to host their own email and basic web services. The administrator needs to set up the external firewall to limit what protocols should be allowed to get to the public part of the company's network. Which ports should the administrator open? (Choose three.)
During a wireless penetration test, a tester detects an access point using WPA2 encryption. Which of the following attacks should be used to obtain the key?
Which tool is used to automate SQL injections and exploit a database by forcing a given web application to connect to another database controlled by a hacker?
Jacob is looking through a traffic log that was captured using Wireshark. Jacob has come across what appears to be SYN requests to an internal computer from a spoofed IP address. What is Jacob seeing here?
You are trying to hijack a telnet session from a victim machine with IP address 10.0.0.5 to Cisco router at 10.0.0.1. You sniff the traffic and attempt to predict the sequence and acknowledgement numbers to successfully hijack the telnet session.
Here is the captured data in tcpdump.
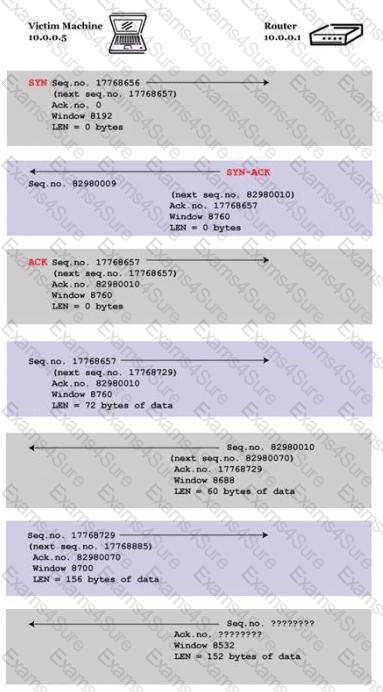
What are the next sequence and acknowledgement numbers that the router will send to the victim machine?
In order to show improvement of security over time, what must be developed?



