
CEH-001 Practice Questions
Certified Ethical Hacker (CEH)
Last Update 3 days ago
Total Questions : 878
Dive into our fully updated and stable CEH-001 practice test platform, featuring all the latest Certified Ethical Hacker CEH exam questions added this week. Our preparation tool is more than just a GAQM study aid; it's a strategic advantage.
Our free Certified Ethical Hacker CEH practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CEH-001. Use this test to pinpoint which areas you need to focus your study on.
Jake is a network administrator who needs to get reports from all the computer and network devices on his network. Jake wants to use SNMP but is afraid that won't be secure since passwords and messages are in clear text. How can Jake gather network information in a secure manner?
You are writing security policy that hardens and prevents Footprinting attempt by Hackers. Which of the following countermeasures will NOT be effective against this attack?
Passive reconnaissance involves collecting information through which of the following?
Which of the following techniques can be used to mitigate the risk of an on-site attacker from connecting to an unused network port and gaining full access to the network? (Choose three.)
June, a security analyst, understands that a polymorphic virus has the ability to mutate and can change its known viral signature and hide from signature-based antivirus programs. Can June use an antivirus program in this case and would it be effective against a polymorphic virus?
User which Federal Statutes does FBI investigate for computer crimes involving e-mail scams and mail fraud?
The following excerpt is taken from a honeyput log. The log captures activities across three days. There are several intrusion attempts; however, a few are successful. Study the log given below and answer the following question:
(Note: The objective of this questions is to test whether the student has learnt about passive OS fingerprinting (which should tell them the OS from log captures): can they tell a SQL injection attack signature; can they infer if a user ID has been created by an attacker and whether they can read plain source – destination entries from log entries.)
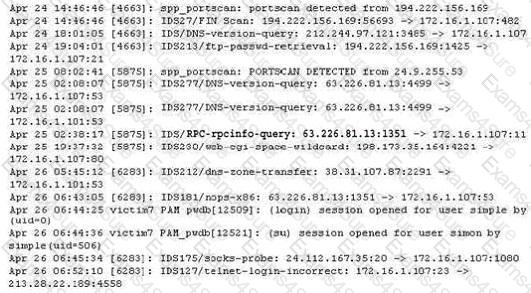
What can you infer from the above log?
What is the essential difference between an ‘Ethical Hacker’ and a ‘Cracker’?
You are having problems while retrieving results after performing port scanning during internal testing. You verify that there are no security devices between you and the target system. When both stealth and connect scanning do not work, you decide to perform a NULL scan with NMAP. The first few systems scanned shows all ports open.
Which one of the following statements is probably true?
War dialing is a very old attack and depicted in movies that were made years ago.
Why would a modem security tester consider using such an old technique?



