
CPEH-001 Practice Questions
Certified Professional Ethical Hacker (CPEH)
Last Update 4 days ago
Total Questions : 736
Dive into our fully updated and stable CPEH-001 practice test platform, featuring all the latest Information Systems Security exam questions added this week. Our preparation tool is more than just a GAQM study aid; it's a strategic advantage.
Our free Information Systems Security practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CPEH-001. Use this test to pinpoint which areas you need to focus your study on.
An attacker is trying to redirect the traffic of a small office. That office is using their own mail server, DNS server and NTP server because of the importance of their job. The attacker gains access to the DNS server and redirects the direction www.google.com to his own IP address. Now when the employees of the office want to go to Google they are being redirected to the attacker machine. What is the name of this kind of attack?
While performing online banking using a Web browser, a user receives an email that contains a link to an interesting Web site. When the user clicks on the link, another Web browser session starts and displays a video of cats playing a piano. The next business day, the user receives what looks like an email from his bank, indicating that his bank account has been accessed from a foreign country. The email asks the user to call his bank and verify the authorization of a funds transfer that took place.
What Web browser-based security vulnerability was exploited to compromise the user?
A company's security policy states that all Web browsers must automatically delete their HTTP browser cookies upon terminating. What sort of security breach is this policy attempting to mitigate?
Which Metasploit Framework tool can help penetration tester for evading Anti-virus Systems?
A hacker has managed to gain access to a Linux host and stolen the password file from /etc/passwd. How can he use it?
You want to do an ICMP scan on a remote computer using hping2. What is the proper syntax?
Todd has been asked by the security officer to purchase a counter-based authentication system. Which of the following best describes this type of system?
An attacker tries to do banner grabbing on a remote web server and executes the following command.
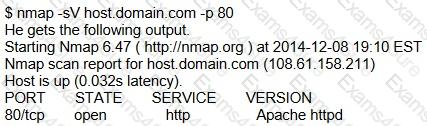
Service detection performed. Please report any incorrect results at http://nmap.org/submit/.
Nmap done: 1 IP address (1 host up) scanned in 6.42 seconds
What did the hacker accomplish?
By using a smart card and pin, you are using a two-factor authentication that satisfies
Sid is a judge for a programming contest. Before the code reaches him it goes through a restricted OS and is tested there. If it passes, then it moves onto Sid. What is this middle step called?



