H12-891_V1.0 Practice Questions
HCIE-Datacom V1.0
Last Update 1 day ago
Total Questions : 322
Dive into our fully updated and stable H12-891_V1.0 practice test platform, featuring all the latest HCIE-Datacom exam questions added this week. Our preparation tool is more than just a Huawei study aid; it's a strategic advantage.
Our free HCIE-Datacom practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about H12-891_V1.0. Use this test to pinpoint which areas you need to focus your study on.
Telemetry data must be encoded in GPB binary format. This format reduces the number of bytes in telemetry messages and improves the transmission efficiency compared with messages encoded in JSON format.
Which of the following statements about BIER (Bit Index Explicit Replication) and PIM (Protocol Independent Multicast) are correct?
Which of the following statements are correct about the command:
ping -aX -cY -sZ -vpn-instance M 10.5.16.2
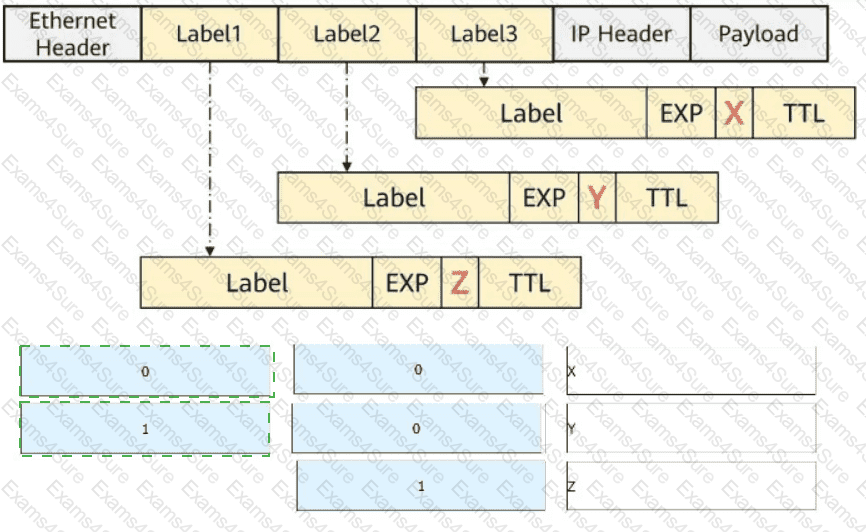
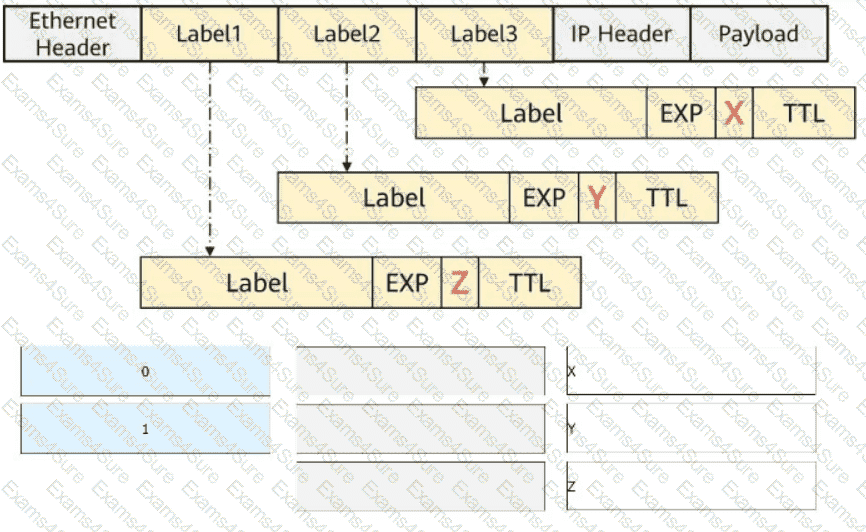
The figure shows a packet that contains three label headers. Select the values (in decimal notation) of the X, Y, and Z fields, respectively.
Huawei Open Programmability System (OPS) uses standard HTTP methods to access managed objects to manage network devices. Which of the following HTTP methods is used to configure the value of a network device ' s managed object?
SR-MPLS is enabled on all routers. The label information encapsulated by R1 into a data packet is shown in the figure.
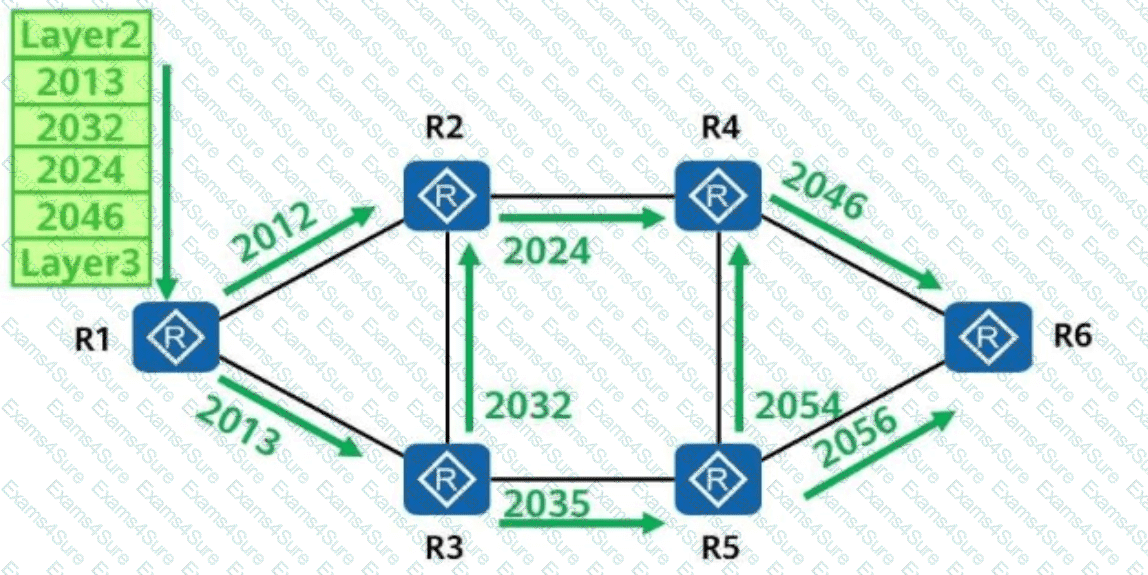
Which of the following is the forwarding path of the data packet?
Which of the following parameters is not included in an IPsec security association (SA)?
When Huawei iMaster NCE-IP is used to configure SR-MPLS TE tunnels, which of the following protocols is used by the controller to collect device running status information?
Which of the following technologies can be used to measure performance based on actual service traffic in Huawei ' s CloudWAN solution?