H12-891_V1.0 Practice Questions
HCIE-Datacom V1.0
Last Update 1 day ago
Total Questions : 322
Dive into our fully updated and stable H12-891_V1.0 practice test platform, featuring all the latest HCIE-Datacom exam questions added this week. Our preparation tool is more than just a Huawei study aid; it's a strategic advantage.
Our free HCIE-Datacom practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about H12-891_V1.0. Use this test to pinpoint which areas you need to focus your study on.
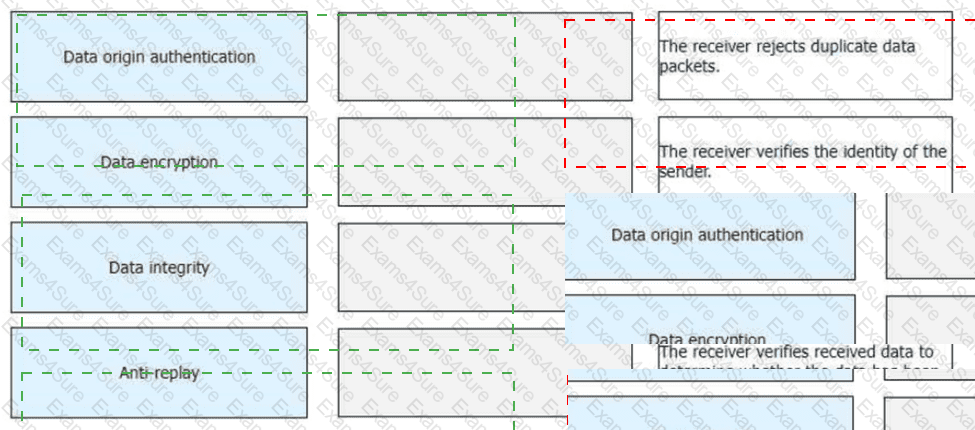
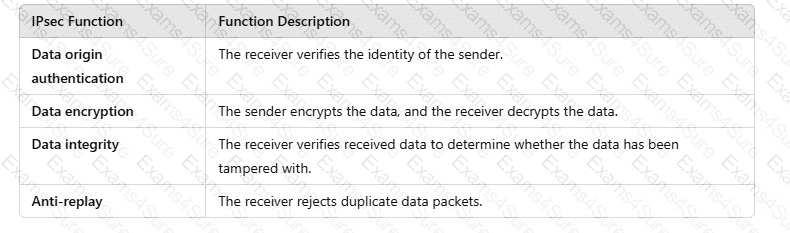
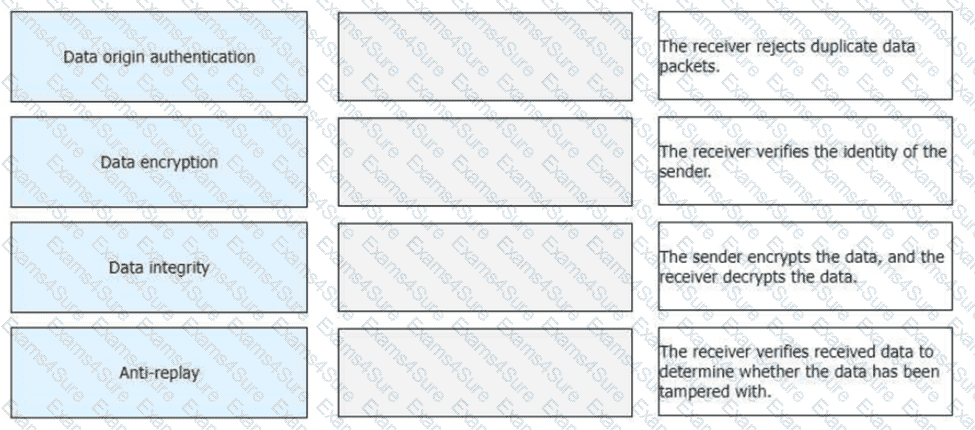
Drag the IPsec functions on the left to the corresponding function description on the right.
How long is an IPv6 prefix assigned to a host when an IPv6 address is configured for the host in SLAAC mode?
Which of the following statements is incorrect about intranet security design for a large or medium-sized virtualized campus network?
For telemetry data push, data can be transferred between devices and collectors using the TLS protocol. TLS must be configured for data encryption if data is pushed based on gRP
C.
If the number of MAC addresses learned on an interface enabled with port security reaches the upper limit, which of the following actions may the switch take?
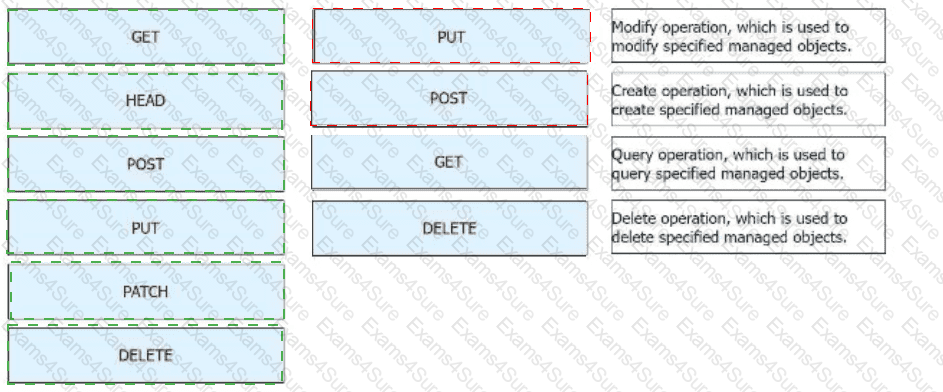
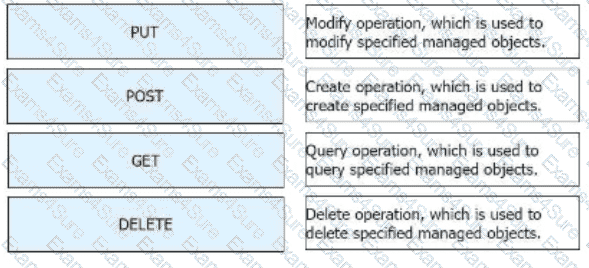
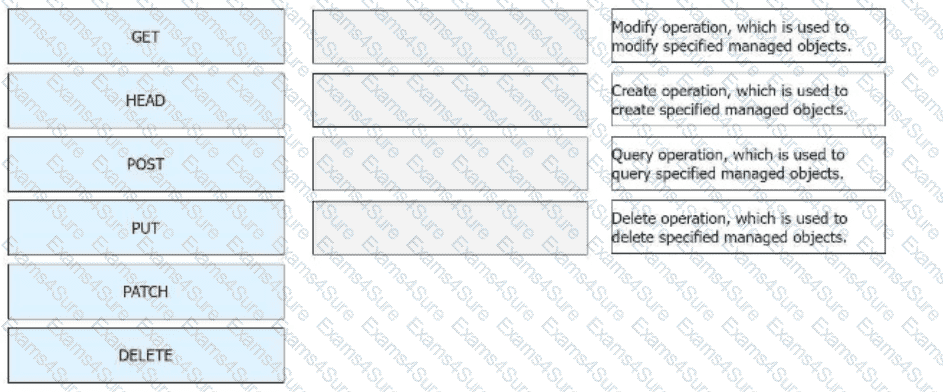
Huawei Open Programmability System (OPS) uses HTTP methods to access managed objects to manage network devices. Drag the HTTP methods to their corresponding functions.
Which of the following is the purpose of configuring IS-IS fragmentation on an IS-IS device?
In BGP4+, what is the content of the next hop network address field carried in the MP_REACH_NLRI attribute of an Update packet?
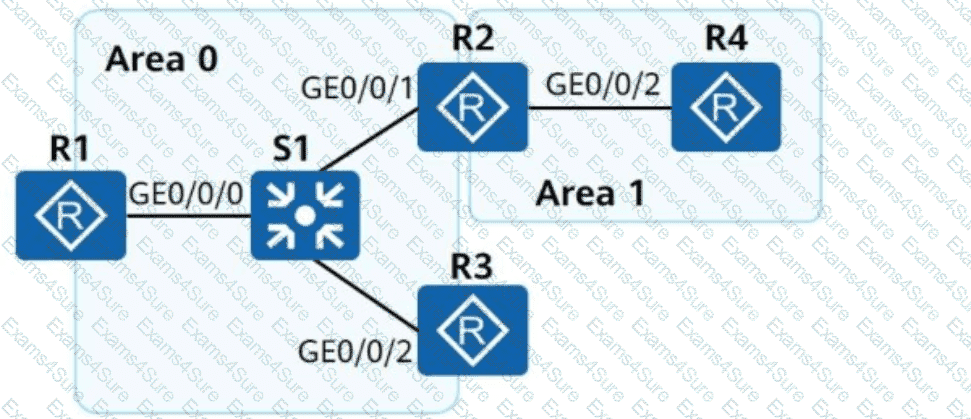
On the campus network shown, IPv6 is deployed for service tests. Four routers are deployed on the network, and these routers use OSPFv3 for network connectivity. Which of the following statements about LSAs generated by the OSPFv3 network is incorrect?
The following figure shows the inter-AS MPLS L3VPN Option C (Solution 2). ASBR-PE2 is connected to CE3 and runs eBGP.
To enable all CEs to communicate with each other, which of the following address families must peer relationships be enabled in the BGP process of ASBR-PE2?