300-215 Practice Questions
Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
Last Update 4 days ago
Total Questions : 131
Dive into our fully updated and stable 300-215 practice test platform, featuring all the latest CyberOps Professional exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CyberOps Professional practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 300-215. Use this test to pinpoint which areas you need to focus your study on.
Refer to the exhibit.
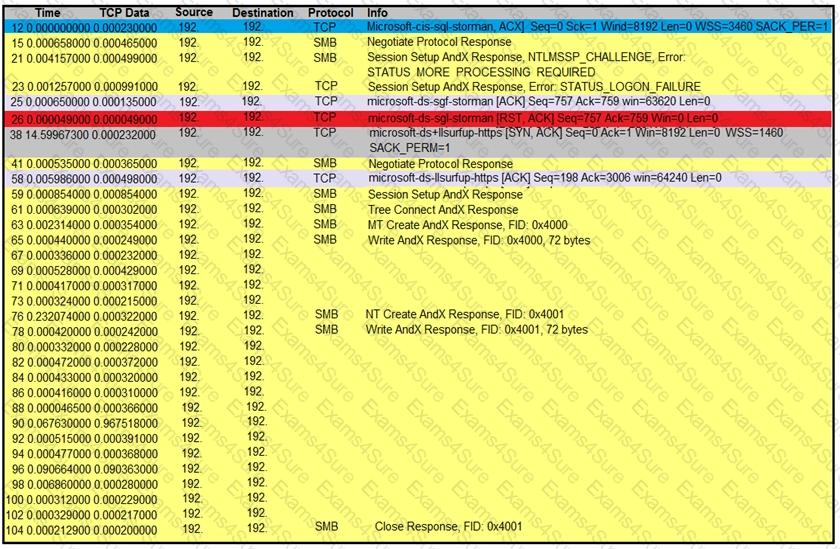
An engineer is analyzing a TCP stream in Wireshark after a suspicious email with a URL. What should be determined about the SMB traffic from this stream?
A malware outbreak revealed that a firewall was misconfigured, allowing external access to the SharePoint server. What should the security team do next?
A new zero-day vulnerability is discovered in the web application. Vulnerability does not require physical access and can be exploited remotely. Attackers are exploiting the new vulnerability by submitting a form with malicious content that grants them access to the server. After exploitation, attackers delete the log files to hide traces. Which two actions should the security engineer take next? (Choose two.)
A financial company handling international transactions recently experienced a complex security incident The incident involves simultaneous DDoS attacks, suspected internal data leakage and the discovery of sophisticated malware implants that have remained dormant until triggered remotely During the incident it became clear that the current procedures are inadequate and plans to tackle issues were created on the go To counter this problem going forward, the IR team is developing an incident playbook to be used if a similar incident reoccurs Which set of elements of the playbook must be introduced?
An organization experienced a sophisticated phishing attack that resulted in the compromise of confidential information from thousands of user accounts. The threat actor used a land and expand approach, where initially accessed account was used to spread emails further. The organization's cybersecurity team must conduct an in-depth root cause analysis to uncover the central factor or factors responsible for the success of the phishing attack. The very first victim of the attack was user with email 500236186@test.com. The primary objective is to formulate effective strategies for preventing similar incidents in the future. What should the cybersecurity engineer prioritize in the root cause analysis report to demonstrate the underlying cause of the incident?
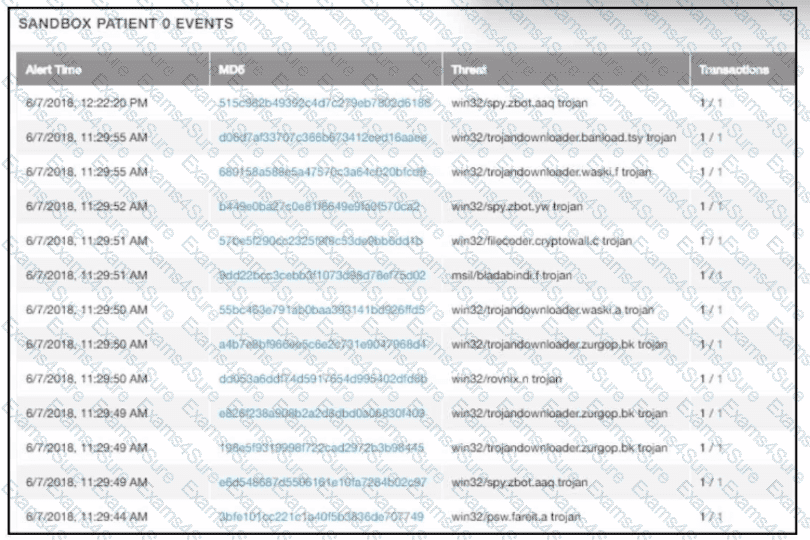
multiple machines behave abnormally. A sandbox analysis reveals malware. What must the administrator determine next?
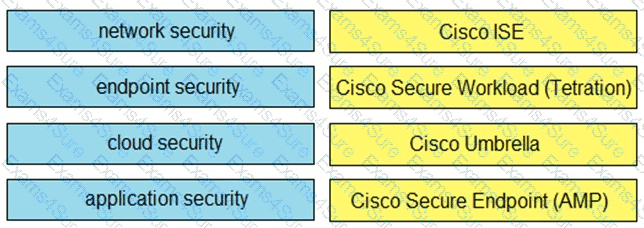
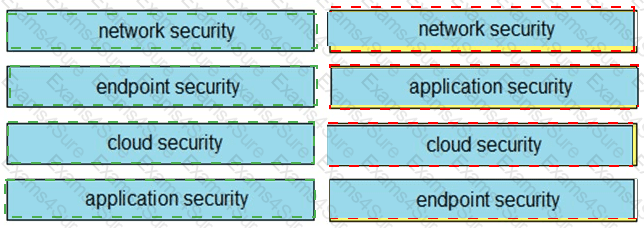
Drag and drop the capabilities on the left onto the Cisco security solutions on the right.