
300-215 Practice Questions
Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
Last Update 4 days ago
Total Questions : 131
Dive into our fully updated and stable 300-215 practice test platform, featuring all the latest CyberOps Professional exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CyberOps Professional practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 300-215. Use this test to pinpoint which areas you need to focus your study on.
Refer to the exhibit.
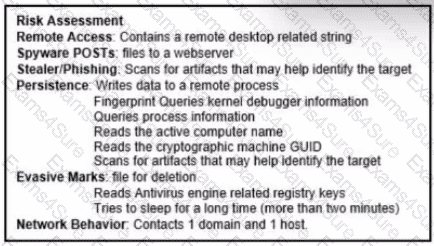
The application x-dosexec with hash 691c65e4fb1d19f82465df1d34ad51aaeceba14a78167262dc7b2840a6a6aa87 is reported as malicious and labeled as "Trojan.Generic" by the threat intelligence tool. What is considered an indicator of compromise?
Refer to the exhibit.
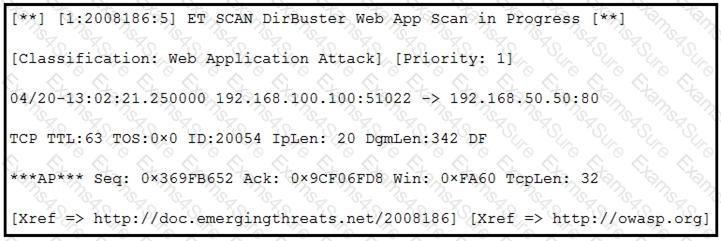
According to the SNORT alert, what is the attacker performing?
An organization experienced a ransomware attack that resulted in the successful infection of their workstations within their network. As part of the incident response process, the organization's cybersecurity team must prepare a comprehensive root cause analysis report. This report aims to identify the primary factor or factors responsible for the successful ransomware attack and to formulate effective strategies to prevent similar incidents in the future. In this context, what should the cybersecurity engineer emphasize in the root cause analysis report to demonstrate the underlying cause of the incident?
What can the blue team achieve by using Hex Fiend against a piece of malware?
Refer to the exhibit.
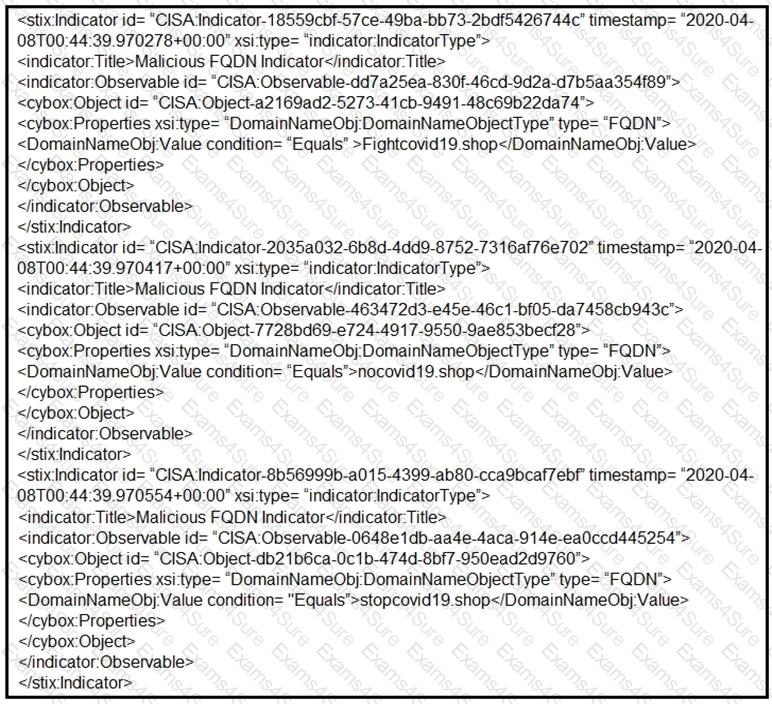
Which two actions should be taken based on the intelligence information? (Choose two.)
An attacker modifies a malicious file named TOPSECRET0523619132 by changing its file extension from a .png to a doc in an attempt to evade detection. Which technique is being used to disguise the file?
Which technique is used to evade detection from security products by executing arbitrary code in the address space of a separate live operation?
A cybersecurity analyst detects fileless malware activity on secure endpoints. What should be done next?
A security team is notified from a Cisco ESA solution that an employee received an advertising email with an attached .pdf extension file. The employee opened the attachment, which appeared to be an empty document. The security analyst cannot identify clear signs of compromise but reviews running processes and determines that PowerShell.exe was spawned by CM
D.
exe with a grandparent AcroRd32.exe process. Which two actions should be taken to resolve this issue? (Choose two.)


