
CAS-005 Practice Questions
CompTIA SecurityX Certification Exam
Last Update 3 days ago
Total Questions : 344
Dive into our fully updated and stable CAS-005 practice test platform, featuring all the latest CompTIA CASP exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free CompTIA CASP practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CAS-005. Use this test to pinpoint which areas you need to focus your study on.
Users must accept the terms presented in a captive petal when connecting to a guest network. Recently, users have reported that they are unable to access the Internet after joining the network A network engineer observes the following:
• Users should be redirected to the captive portal.
• The Motive portal runs Tl. S 1 2
• Newer browser versions encounter security errors that cannot be bypassed
• Certain websites cause unexpected re directs
Which of the following mow likely explains this behavior?
A company that uses several cloud applications wants to properly identify:
All the devices potentially affected by a given vulnerability.
All the internal servers utilizing the same physical switch.
The number of endpoints using a particular operating system.Which of the following is the best way to meet the requirements?
A compliance officer isfacilitating abusiness impact analysis (BIA)and wantsbusiness unit leadersto collect meaningful data. Several business unit leaders want more information about the types of data the officer needs.
Which of the following data types would be the most beneficial for the compliance officer?(Select two)
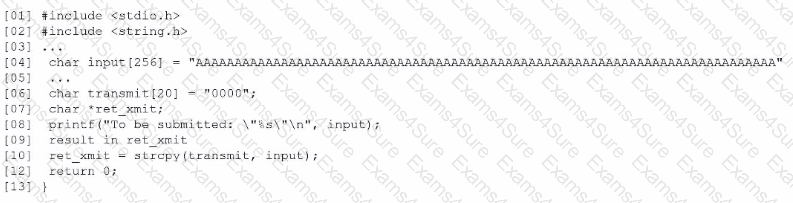
Based on the results of a SAST report on a legacy application, a security engineer is reviewing the following snippet of code flagged as vulnerable:
Which of the following is the vulnerable line of code that must be changed?
Which of the following includes best practices for validating perimeter firewall configurations?
A security analyst needs to ensure email domains that send phishing attempts without previous communications are not delivered to mailboxes The following email headers are being reviewed
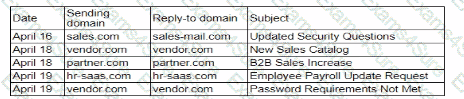
Which of thefollowing is the best action for the security analyst to take?
A security engineer is developing a solution to meet the following requirements?
• All endpoints should be able to establish telemetry with a SIEM.
• All endpoints should be able to be integrated into the XDR platform.
• SOC services should be able to monitor the XDR platform
Which of the following should the security engineer implement to meet the requirements?
A global manufacturing company has an internal application mat is critical to making products This application cannot be updated and must Beavailable in the production area A security architect is implementing security for the application. Which of the following best describes the action the architect should take-?
A software engineer is creating a CI/CD pipeline to support the development of a web application The DevSecOps team is required to identify syntax errors Which of the following is the most relevant to the DevSecOps team's task'
The device event logs sourced from MDM software are as follows:
Device | Date/Time | Location | Event | Description
ANDROID_102 | 01JAN21 0255 | 38.9072N, 77.0369W | PUSH | APPLICATION 1220 INSTALL QUEUED
ANDROID_102 | 01JAN21 0301 | 38.9072N, 77.0369W | INVENTORY | APPLICATION 1220 ADDED
ANDROID_1022 | 01JAN21 0701 | 39.0067N, 77.4291W | CHECK-IN | NORMAL
ANDROID_1022 | 01JAN21 0701 | 25.2854N, 51.5310E | CHECK-IN | NORMAL
ANDROID_1022 | 01JAN21 0900 | 39.0067N, 77.4291W | CHECK-IN | NORMAL
ANDROID_1022 | 01JAN21 1030 | 39.0067N, 77.4291W | STATUS | LOCAL STORAGE REPORTING 85% FULL
Which of the following security concerns and response actions would best address the risks posed by the device in the logs?



