
CAS-005 Practice Questions
CompTIA SecurityX Certification Exam
Last Update 3 days ago
Total Questions : 344
Dive into our fully updated and stable CAS-005 practice test platform, featuring all the latest CompTIA CASP exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free CompTIA CASP practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CAS-005. Use this test to pinpoint which areas you need to focus your study on.
A Chief Information Security Officer (CISO) is concerned that a company's current data disposal procedures could result in data remanence. The company uses only SSDs. Which of the following would be the most secure way to dispose of the SSDs given the CISO's concern?
During a recent security event, access from the non-production environment to the production environment enabled unauthorized users to install unapproved software and make unplanned configuration changes. During an investigation, the following findings are identified:
• Several new users were added in bulk by the IAM team.
• Additional firewalls and routers were recently added to the network.
• Vulnerability assessments have been disabled for all devices for more than 30 days.
• The application allow list has not been modified in more than two weeks.
• Logs were unavailable for various types of traffic.
• Endpoints have not been patched in more than ten days.
Which of the following actions would most likely need to be taken to ensure proper monitoring is in place within the organization? (Select two)
A security engineer performed a code scan that resulted in many false positives. The security engineer must find asolution that improves the quality of scanning results before application deployment. Which of the following is the best solution?
Due to an infrastructure optimization plan, a company has moved from a unified architecture to a federated architecture divided by region. Long-term employees now have a better experience, but new employees are experiencing major performance issues when traveling between regions. The company is reviewing the following information:
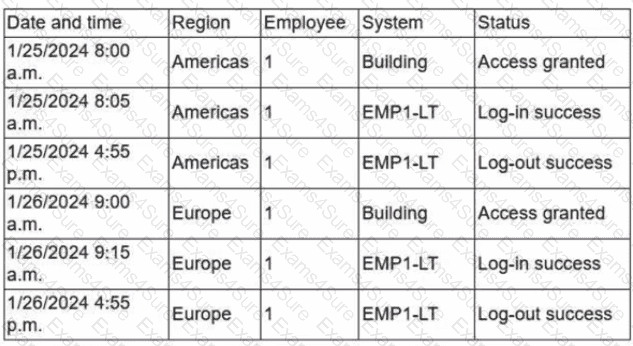
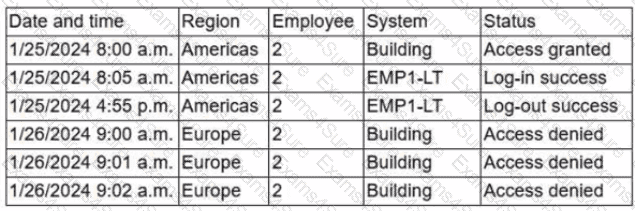
Which of the following is the most effective action to remediate the issue?
A security engineer wants to reduce the attack surface of a public-facing containerized application Which of the following will best reduce the application's privilege escalation attack surface?
A user reports application access issues to the help desk. The help desk reviews the logs for the user
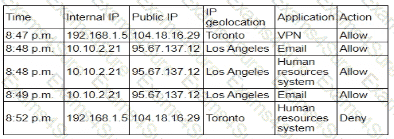
Which of the following is most likely The reason for the issue?
While performing threat-hunting functions, an analyst is using the Diamond Model of Intrusion Analysis. The analyst identifies the likely adversary, the infrastructure involved, and the target. Which of the following must the threat hunter document to use the model effectively?
An organization determines existing business continuity practices are inadequate to support critical internal process dependencies during a contingency event. A compliance analyst wants the Chief Information Officer (CIO) to identify the level of residual risk that is acceptable to guide remediation activities. Which of the following does the CIO need to clarify?
A security analyst isreviewing the following event timeline from an COR solution:
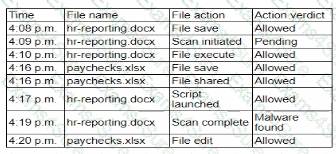
Which of the following most likely has occurred and needs to be fixed?
An organization mat performs real-time financial processing is implementing a new backup solution Given the following business requirements?
* The backup solution must reduce the risk for potential backup compromise
* The backup solution must be resilient to a ransomware attack.
* The time to restore from backups is less important than the backup data integrity
* Multiple copies of production data must be maintained
Which of the following backup strategies best meets these requirement?



