ISO-IEC-27001-Lead-Auditor Practice Questions
PECB Certified ISO/IEC 27001 2022 Lead Auditor exam
Last Update 4 days ago
Total Questions : 418
Dive into our fully updated and stable ISO-IEC-27001-Lead-Auditor practice test platform, featuring all the latest ISO 27001 exam questions added this week. Our preparation tool is more than just a PECB study aid; it's a strategic advantage.
Our free ISO 27001 practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about ISO-IEC-27001-Lead-Auditor. Use this test to pinpoint which areas you need to focus your study on.
The data centre at which you work is currently seeking ISO/IEC27001:2022 certification. In preparation for your initial certification visit, several internal audits have been carried out by a colleague working at another data centre within your Group. They secured their own ISO/IEC 27001:2022 certificate earlier in the year.
You have just qualified as an Internal ISMS auditor and your manager has asked you to review the audit process and audit findings as a final check before the external Certification Body arrives.
Which four of the following would cause you concern in respect of conformity to ISO/IEC 27001:2022 requirements?
Question
A retail company experienced a malware infection that bypassed its existing security measures. To minimize damage, remove the malware, and restore affected systems to normal operation, what type of controls should the company implement?
You are performing an ISMS audit at a residential nursing home called ABC that provides healthcare services. You find all nursing home residents wear an electronic wristband for monitoring their location, heartbeat, and blood pressure always. You learned that the electronic wristband automatically uploads all data to the artificial intelligence (AI) cloud server for healthcare monitoring and analysis by healthcare staff.
To verify the scope of ISMS, you interview the management system representative (MSR) who explains that the ISMS scope covers an outsourced data center.
Select three options for the audit evidence you need to find to verify the scope of the ISMS.
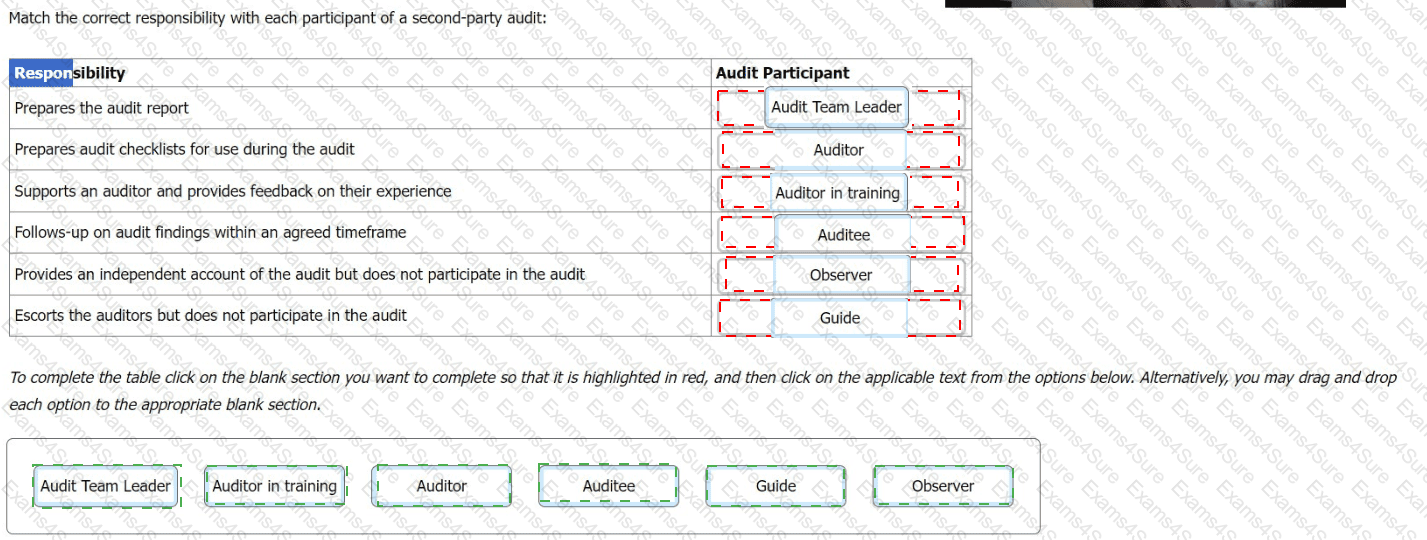
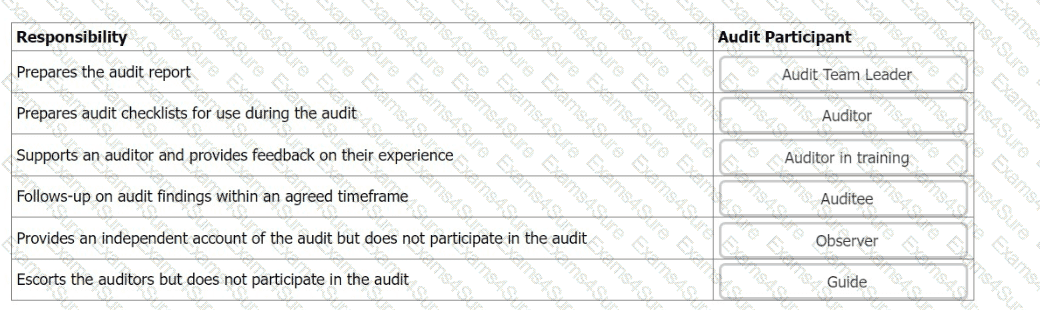
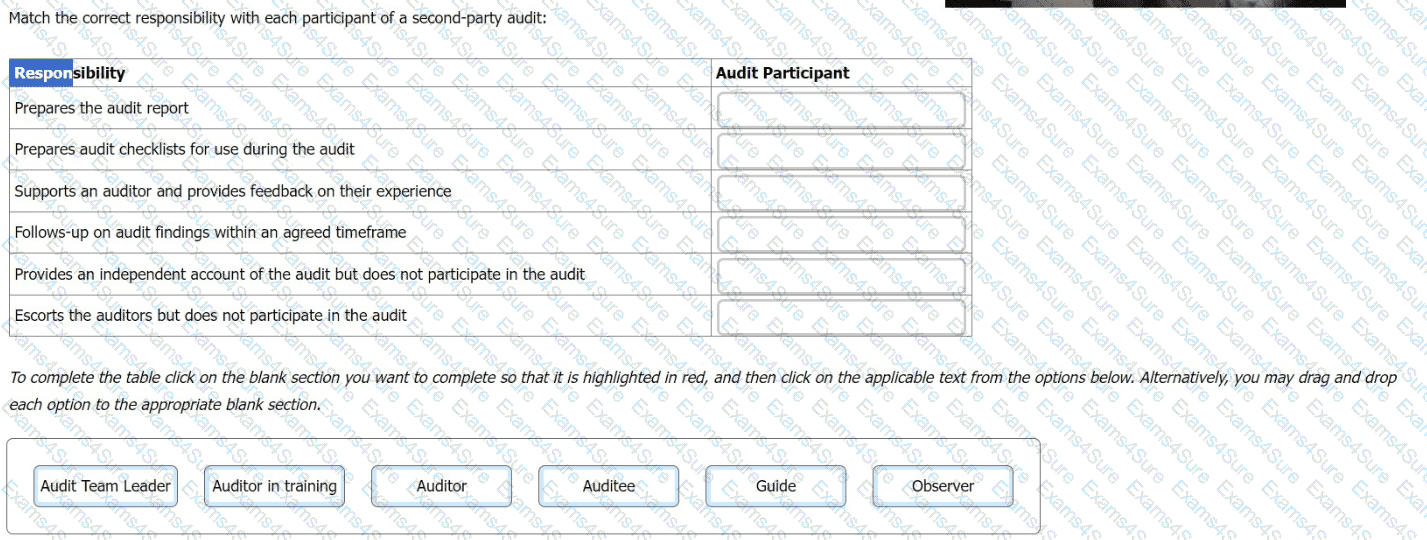
Match the correct responsibility with each participant of a second-party audit:
Scenario 4
SendPay is a financial services company specializing in global money transfers through a network of agents and institutions. As a new company in the market, SendPay aims to deliver top-quality services with its fee-free digital platform, launched last year, enabling clients to send and receive money anytime via smartphones and laptops. At that time, SendPay outsourced software operations to an external team, which also managed the company's technology infrastructure.
Recently, the company applied for ISO/IEC 27001 certification after having an ISMS in place for almost a year.
During the audit, the auditors focused on reviewing SendPay’s outsourced operations, specifically looking at the software development and technology infrastructure maintenance handled by the outsourced company. They followed a structured approach, which included reviewing and evaluating SendPay’s processes for monitoring the quality of these outsourced operations. This included verifying if the company met its contractual obligations, ensuring proper governance procedures for engaging outsourced entities, and assessing SendPay’s plans in case of expected or unexpected termination of outsourcing agreements.
However, the auditors subtly noted that SendPay’s protocols did not fully address contingencies for unanticipated cancellations of outsourcing agreements. Additionally, a technical expert appointed by SendPay assisted the auditors, providing specific knowledge and expertise related to the outsourced operations being audited.
The audit team calculated the number of training hours employees received on ISMS to ensure alignment with established objectives. They also computed the average resolution time of information security incidents based on a sample taken during the audit, which provided valuable insights into SendPay’s incident management practices. In addition, the auditors evaluated the reliability of the evidence collected during the audit. They considered several factors influencing the reliability of audit evidence. For example, evidence from surveillance cameras provided more objective proof compared to photos. Timing also played a crucial role in reliability, with mechanisms like transaction recording enhancing the credibility of the evidence.
SendPay uses cloud-based platforms to make its operations more efficient and scalable. However, during the audit, the auditors did not request SendPay to provide an inventory of their cloud activities due to resource limitations, relying instead on SendPay’s representations.
Question
Based on Scenario 4, is the involvement of all the parties acceptable during the auditing of the outsourced operations?
Scenario:
Northstorm is an online retail shop offering unique vintage and modern accessories. It initially entered a small market but gradually grew thanks to the development of the overall e-commerce landscape. Northstorm works exclusively online and ensures efficient payment processing, inventory management, marketing tools, and shipment orders. It uses prioritized ordering to receive, restock, and ship its most popular products.
Northstorm has traditionally managed its IT operations by hosting its website and maintaining full control over its infrastructure, including hardware, software, and data administration. However, this approach hindered its growth due to the lack of responsive infrastructure. Seeking to enhance its e-commerce and payment systems, Northstorm opted to expand its in-house data centers, completing the expansion in two phases over three months. Initially, the company upgraded its core servers, point-of-sale, ordering, billing, database, and backup systems. The second phase involved improving mail, payment, and network functionalities. Additionally, during this phase, Northstorm adopted an international standard for personally identifiable information (PII) controllers and PII processors regarding PII processing to ensure its data handling practices were secure and compliant with global regulations.
Despite the expansion, Northstorm's upgraded data centers failed to meet its evolving business demands. This inadequacy led to several new challenges, including issues with order prioritization. Customers reported not receiving priority orders, and the company struggled with responsiveness. This was largely due to the main server's inability to process orders from YouDecide, an application designed to prioritize orders and simulate customer interactions. The application, reliant on advanced algorithms, was incompatible with the new operating system (OS) installed during the upgrade.
Faced with urgent compatibility issues, Northstorm quickly patched the application without proper validation, leading to the installation of a compromised version. This security lapse resulted in the main server being affected and the company's website going offline for a week. Recognizing the need for a more reliable solution, the company decided to outsource its website hosting to an e-commerce provider. The company signed a confidentiality agreement concerning product ownership and conducted a thorough review of user access rights to enhance security before transitioning.
Question:
Which of the following is a preventive control based on Scenario 1?
Question:
EquiBank is undergoing an external audit of its financial management system. The auditors evaluate the logic of transactions processed by EquiBank's financial software. To ensure accuracy, they use simulations to validate operations, calculations, and controls programmed in the software applications. What type of Computer-Assisted Audit Technique (CAAT) is used?
Scenario 6
Sinvestment is an insurance provider that offers a wide range of coverage options, including home, commercial, and life insurance. Originally established in North California, the company has expanded its operations to other locations, including Europe and Africa. In addition to its growth, Sinvestment is committed to complying with laws and regulations applicable to its industry and preventing any information security incident. They have implemented an information security management system (ISMS) based on ISO/IEC 27001 and have applied for certification.
A team of auditors was assigned by the certification body to conduct the audit. After signing a confidentiality agreement with Sinvestment, they started the audit activities. For the activities of the stage 1 audit, it was decided that they would be performed on site, except the review of documented information, which took place remotely, as requested by Sinvestment.
The audit team started the stage 1 audit by reviewing the documentation required, including the declaration of the ISMS scope, information security policies, and internal audit reports. The evaluation of the documented information was based on the content and procedure for managing the documented information.
In addition, the auditors found out that the documentation related to information security training and awareness programs was incomplete and lacked essential details. When asked, Sinvestment’s top management stated that the company has provided information security training sessions to all employees.
The stage 2 audit was conducted three weeks after the stage 1 audit. The audit team observed that the marketing department (not included in the audit scope) had no procedures to control employees’ access rights. Since controlling employees' access rights is one of the ISO/IEC 27001 requirements and was included in the company's information security policy, the issue was included in the audit report.
Question
According to Scenario 6, was it appropriate for the audit team to include in the audit report the observed deficiency in the marketing department's access rights control procedures?