ISO-IEC-27001-Lead-Auditor Practice Questions
PECB Certified ISO/IEC 27001 2022 Lead Auditor exam
Last Update 4 days ago
Total Questions : 418
Dive into our fully updated and stable ISO-IEC-27001-Lead-Auditor practice test platform, featuring all the latest ISO 27001 exam questions added this week. Our preparation tool is more than just a PECB study aid; it's a strategic advantage.
Our free ISO 27001 practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about ISO-IEC-27001-Lead-Auditor. Use this test to pinpoint which areas you need to focus your study on.
Question:
Which of the following statements regarding threats and vulnerabilities in information security is NOT correct?
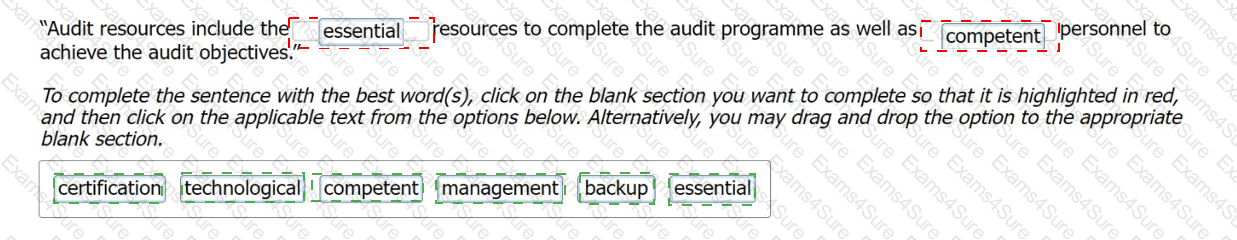
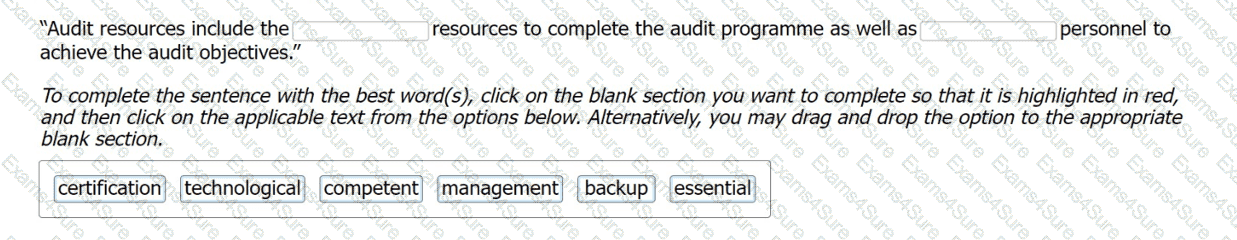
Select the words that best complete the sentence below to describe audit resources:
Which two of the following are examples of audit methods that 'do not' involve human interaction?
Conducting an interview using a teleconferencing platform
Question
An organization scheduled an internal audit to evaluate the ISMS effectiveness. However, it did not define the audit scope and clear audit objectives. As a result, the internal auditor overlooked critical departments handling sensitive information.
What risk associated with the audit program was present in this scenario?
Scenario 8: EsBank provides banking and financial solutions to the Estonian banking sector since September 2010. The company has a network of 30 branches with over 100 ATMs across the country.
Operating in a highly regulated industry, EsBank must comply with many laws and regulations regarding the security and privacy of data. They need to manage information security across their operations by implementing technical and nontechnical controls. EsBank decided to implement an ISMS based on ISO/IEC 27001 because it provided better security, more risk control, and compliance with key requirements of laws and regulations.
Nine months after the successful implementation of the ISMS, EsBank decided to pursue certification of their ISMS by an independent certification body against ISO/IEC 27001 .The certification audit included all of EsBank’s systems, processes, and technologies.
The stage 1 and stage 2 audits were conducted jointly and several nonconformities were detected. The first nonconformity was related to EsBank’s labeling of information. The company had an information classification scheme but there was no information labeling procedure. As a result, documents requiring the same level of protection would be labeled differently (sometimes as confidential, other times sensitive).
Considering that all the documents were also stored electronically, the nonconformity also impacted media handling. The audit team used sampling and concluded that 50 of 200 removable media stored sensitive information mistakenly classified as confidential. According to the information classification scheme, confidential information is allowed to be stored in removable media, whereas storing sensitive information is strictly prohibited. This marked the other nonconformity.
They drafted the nonconformity report and discussed the audit conclusions with EsBank’s representatives, who agreed to submit an action plan for the detected nonconformities within two months.
EsBank accepted the audit team leader's proposed solution. They resolved the nonconformities by drafting a procedure for information labeling based on the classification scheme for both physical and electronic formats. The removable media procedure was also updated based on this procedure.
Two weeks after the audit completion, EsBank submitted a general action plan. There, they addressed the detected nonconformities and the corrective actions taken, but did not include any details on systems, controls, or operations impacted. The audit team evaluated the action plan and concluded that it would resolve the nonconformities. Yet, EsBank received an unfavorable recommendation for certification.
Based on the scenario above, answer the following question:
Based on scenario 8, EsBank submitted a general action plan. Is this acceptable?
Scenario 5
CyberShielding Systems Inc. provides security services spanning the entire information technology infrastructure. It provides cybersecurity software, including endpoint security, firewalls, and antivirus software. CyberShielding Systems Inc. has helped various companies secure their networks for two decades through advanced products and services. Having achieved a reputation in the information and network security sector, CyberShielding Systems Inc. decided to implement a security information management system (ISMS) based on ISO/IEC 27001 and obtain a certification to better secure its internal and customer assets and gain a competitive advantage.
The certification body initiated the process by selecting the audit team for CyberShielding Systems Inc.'s ISO/IEC 27001 certification. They provided the company with the name and background information of each audit member. However, upon review, CyberShielding Systems Inc. discovered that one of the auditors did not hold the security clearance required by them. Consequently, the company objected to the appointment of this auditor. Upon review, the certification body replaced the auditor in response to CyberShielding Systems Inc.'s objection.
As part of the audit process, CyberShielding Systems Inc.'s approach to risk and opportunity determination was assessed as a standalone activity. This involved examining the organization’s methods for identifying and managing risks and opportunities. The audit team’s core objectives encompassed providing assurance on the effectiveness of CyberShielding Systems Inc.'s risk and opportunity identification mechanisms and reviewing the organization's strategies for addressing these determined risks and opportunities. During this, the audit team also identified a risk due to a lack of oversight in the firewall configuration review process, where changes were implemented without proper approval, potentially exposing the company to vulnerabilities. This finding highlighted the need for stronger internal controls to prevent such issues.
The audit team accessed process descriptions and organizational charts to understand the main business processes and controls. They performed a limited analysis of the IT risks and controls because their access to the IT infrastructure and applications was limited by third-party service provider restrictions. However, the audit team stated that the risk of a significant defect occurring in CyberShielding’s ISMS was low since most of the company's processes were automated. They therefore evaluated that the ISMS, as a whole, conforms to the standard requirements by questioning CyberShielding representatives on IT responsibilities, control effectiveness, and anti-malware measures. CyberShielding’s representatives provided sufficient and appropriate evidence to address all these questions.
Despite the agreement signed before the audit, which outlined the audit scope, criteria, and objectives, the audit was primarily focused on assessing conformity with established criteria and ensuring compliance with statutory and regulatory requirements.
Question
What kind of audit risk did the audit team identify? Refer to Scenario 5.
You have to carry out a third-party virtual audit. Which two of the following issues would you need to inform the auditee about before you start conducting the audit ?
You will ask to see the ID card of the person that is on the screen.
Scenario 1: Fintive is a distinguished security provider for online payments and protection solutions. Founded in 1999 by Thomas Fin in San Jose, California, Fintive
offers services to companies that operate online and want to improve their information security, prevent fraud, and protect user information such as PII. Fintive centers
its decision-making and operating process based on previous cases. They gather customer data, classify them depending on the case, and analyze them. The company
needed a large number of employees to be able to conduct such complex analyses. After some years, however, the technology that assists in conducting such analyses
advanced as well. Now, Fintive is planning on using a modern tool, a chatbot, to achieve pattern analyses toward preventing fraud in real-time. This tool would also be
used to assist in improving customer service.
This initial idea was communicated to the software development team, who supported it and were assigned to work on this project. They began integrating the chatbot
on their existing system. In addition, the team set an objective regarding the chatbot which was to answer 85% of all chat queries.
After the successful integration of the chatbot, the company immediately released it to their customers for use. The chatbot, however, appeared to have some issues.
Due to insufficient testing and lack of samples provided to the chatbot during the training phase, in which it was supposed "to learn" the queries pattern, the chatbot
failed to address user queries and provide the right answers. Furthermore, the chatbot sent random files to users when it received invalid inputs such as odd patterns
of dots and special characters. Therefore, the chatbot was unable to properly answer customer queries and the traditional customer support was overwhelmed with
chat queries and thus was unable to help customers with their requests.
Consequently, Fintive established a software development policy. This policy specified that whether the software is developed in-house or outsourced, it will undergo a
black box testing prior to its implementation on operational systems.
Based on this scenario, answer the following question:
Insufficient testing and lack of samples provided to Fintive's chatbot during the training phase are considered as 1.
Refer to scenario