ISO-IEC-27001-Lead-Auditor Practice Questions
PECB Certified ISO/IEC 27001 2022 Lead Auditor exam
Last Update 4 days ago
Total Questions : 418
Dive into our fully updated and stable ISO-IEC-27001-Lead-Auditor practice test platform, featuring all the latest ISO 27001 exam questions added this week. Our preparation tool is more than just a PECB study aid; it's a strategic advantage.
Our free ISO 27001 practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about ISO-IEC-27001-Lead-Auditor. Use this test to pinpoint which areas you need to focus your study on.
Scenario 2:
Clinic, founded in the 1990s, is a medical device company that specializes in treatments for heart-related conditions and complex surgical interventions. Based in Europe, it serves both patients and healthcare professionals. Clinic collects patient data to tailor treatments, monitor outcomes, and improve device functionality. To enhance data security and build trust, Clinic is implementing an information security management system (ISMS) based on ISO/IEC 27001. This initiative demonstrates Clinic's commitment to securely managing sensitive patient information and proprietary technologies.
Clinic established the scope of its ISMS by solely considering internal issues, interfaces, dependencies between internal and outsourced activities, and the expectations of interested parties. This scope was carefully documented and made accessible. In defining its ISMS, Clinic chose to focus specifically on key processes within critical departments such as Research and Development, Patient Data Management, and Customer Support.
Despite initial challenges, Clinic remained committed to its ISMS implementation, tailoring security controls to its unique needs. The project team excluded certain Annex A controls from ISO/IEC 27001 while incorporating additional sector-specific controls to enhance security. The team evaluated the applicability of these controls against internal and external factors, culminating in the development of a comprehensive Statement of Applicability (SoA) detailing the rationale behind control selection and implementation.
As preparations for certification progressed, Brian, appointed as the team leader, adopted a self-directed risk assessment methodology to identify and evaluate the company’s strategic issues and security practices. This proactive approach ensured that Clinic’s risk assessment aligned with its objectives and mission.
Question:
Based on Scenario 2, the Clinic decided that the ISMS would cover only key processes and departments. Is this acceptable?
The audit team leader decided to involve a technical expert as part of the audit team, so they could fill the potential gaps of the audit team members' knowledge. What should the audit team leader consider in this case?
Question
Which statement best describes how internal audits and external audits complement each other in an organization?
Question
An organization depends on a single server to manage all incoming traffic, creating a potential single point of failure. If the server experiences malfunction or downtime, it could disrupt services.
What does this scenario present, and which aspect of information security is primarily affected?
Scenario 7: Webvue. headquartered in Japan, is a technology company specializing in the development, support, and maintenance of computer software. Webvue provides solutions across various technology fields and business sectors. Its flagship service is CloudWebvue, a comprehensive cloud computing platform offering storage, networking, and virtual computing services. Designed for both businesses and individual users. CloudWebvue is known for its flexibility, scalability, and reliability.
Webvue has decided to only include CloudWebvue in its ISO/IEC 27001 certification scope. Thus, the stage 1 and 2 audits were performed simultaneously Webvue takes pride in its strictness regarding asset confidentiality They protect the information stored in CloudWebvue by using appropriate cryptographic controls. Every piece of information of any classification level, whether for internal use. restricted, or confidential, is first encrypted with a unique corresponding hash and then stored in the cloud
The audit team comprised five persons Keith. Sean. Layla, Sam. and Tina. Keith, the most experienced auditor on the IT and information security auditing team, was the audit team leader. His responsibilities included planning the audit and managing the audit team. Sean and Layla were experienced in project planning, business analysis, and IT systems (hardware and application) Their tasks included audit planning according to Webvue’s internal systems and processes Sam and Tina, on the other hand, who had recently completed their education, were responsible for completing the day-to-day tasks while developing their audit skills
While verifying conformity to control 8.24 Use of cryptography of ISO/IEC 27001 Annex A through interviews with the relevant staff, the audit team found out that the cryptographic keys have been initially generated based on random bit generator (RBG) and other best practices for the generation of the cryptographic keys. After checking Webvue's cryptography policy, they concluded that the information obtained by the interviews was true. However, the cryptographic keys are still in use because the policy does not address the use and lifetime of cryptographic keys.
As later agreed upon between Webvue and the certification body, the audit team opted to conduct a virtual audit specifically focused on verifying conformity to control 8.11 Data Masking of ISO/IEC 27001 within Webvue, aligning with the certification scope and audit objectives. They examined the processes involved in protecting data within CloudWebvue. focusing on how the company adhered to its policies and regulatory standards. As part of this process. Keith, the audit team leader, took screenshot copies of relevant documents and cryptographic key management procedures to document and analyze the effectiveness of Webvue's practices.
Webvue uses generated test data for testing purposes. However, as determined by both the interview with the manager of the QA Department and the procedures used by this department, sometimes live system data are used. In such scenarios, large amounts of data are generated while producing more accurate results. The test data is protected and controlled, as verified by the simulation of the encryption process performed by Webvue's personnel during the audit
While interviewing the manager of the QA Department, Keith observed that employees in the Security Training Department were not following proper procedures, even though this department fell outside the audit scope. Despite the exclusion in the audit scope, the non conformity in the Security Training Department has potential implications for the processes within the audit scope, specifically impacting data security and cryptographic practices in CloudWebvue. Therefore, Keith incorporated this finding into the audit report and accordingly informed the auditee.
Based on the scenario above, answer the following question:
Question:
To verify conformity to the protection of test data control, Webvue’s personnel simulated the encryption process. Is this acceptable?
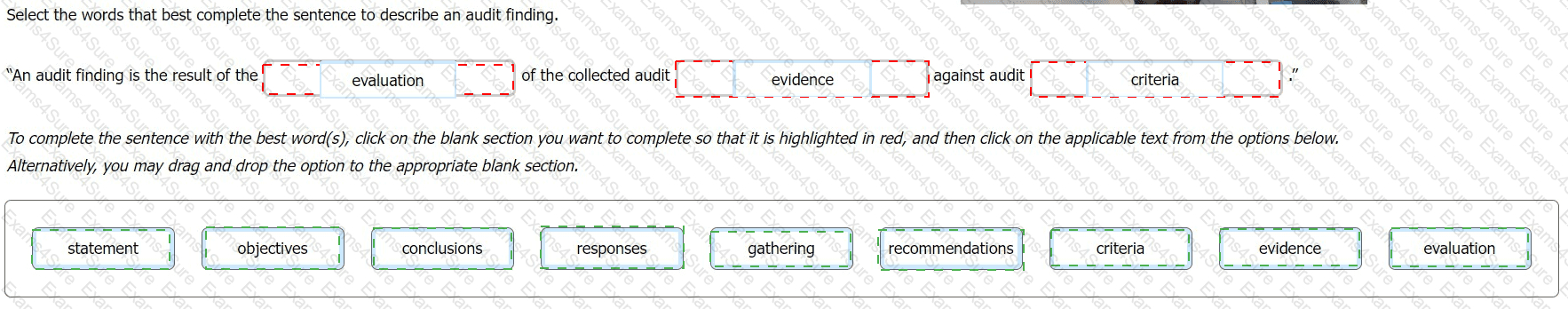
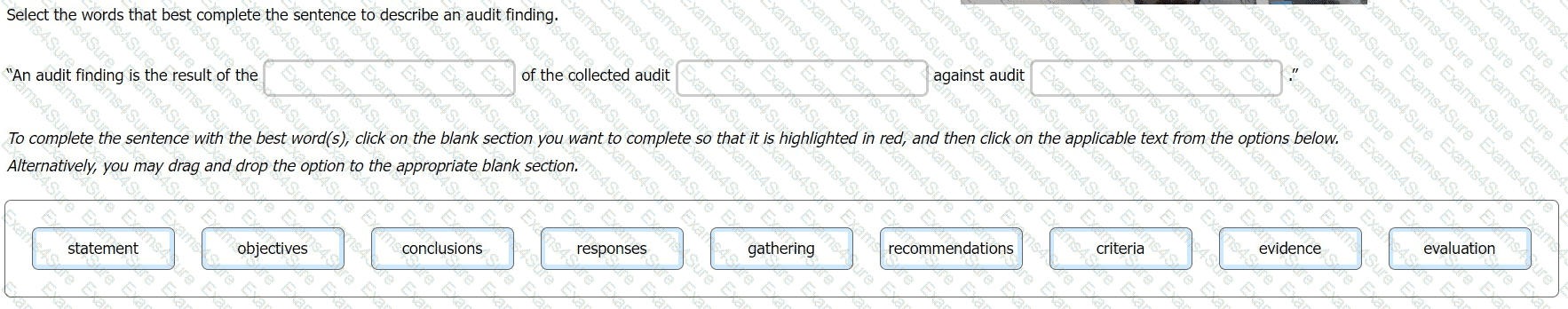
Select the words that best complete the sentence to describe an audit finding.
You are an experienced ISMS audit team leader conducting a third-party surveillance visit.
You notice that although the auditee is claiming conformity with ISO/IEC 27001:2022 they are still referring to Improvement as clause 10.2 (as it was in the 2013 edition) when this is now clause 10.1 in
the 2022 edition. You have confirmed they are meeting all of the 2022 requirements set out in the standard.
Select one option of the action you should take.
You are an ISMS audit team leader tasked with conducting a follow-up audit at a client's data centre. Following two days on-site you conclude that of the original 12 minor and 1 major nonconformities that prompted the follow-up audit, only 1 minor nonconformity still remains outstanding.
Select four options for the actions you could take.
Question:
When multiple offices of a certification body are involved, what must be ensured?