ISO-IEC-27001-Lead-Auditor Practice Questions
PECB Certified ISO/IEC 27001 2022 Lead Auditor exam
Last Update 4 days ago
Total Questions : 418
Dive into our fully updated and stable ISO-IEC-27001-Lead-Auditor practice test platform, featuring all the latest ISO 27001 exam questions added this week. Our preparation tool is more than just a PECB study aid; it's a strategic advantage.
Our free ISO 27001 practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about ISO-IEC-27001-Lead-Auditor. Use this test to pinpoint which areas you need to focus your study on.
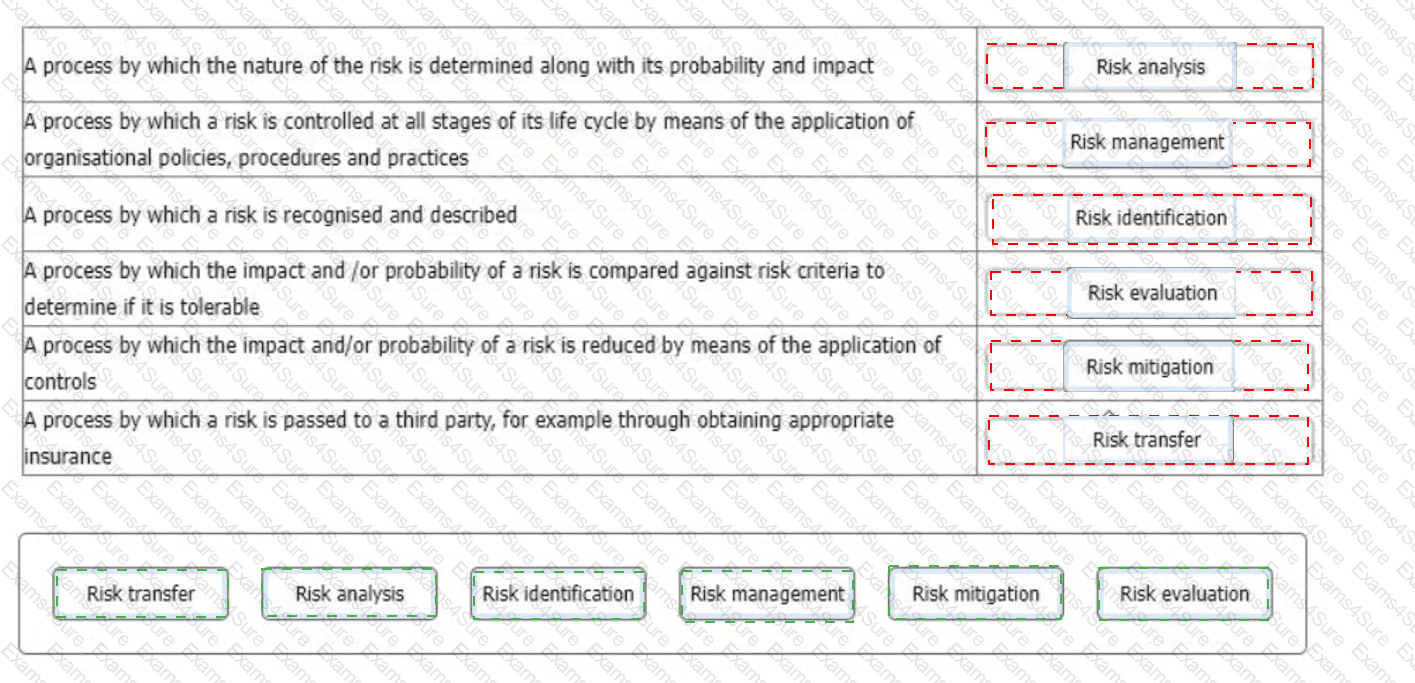
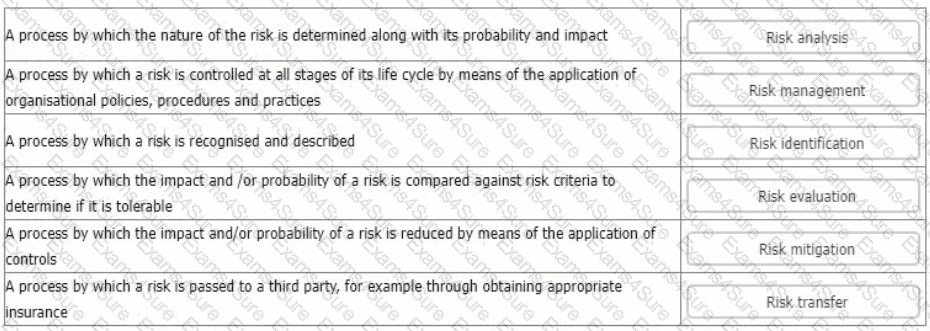
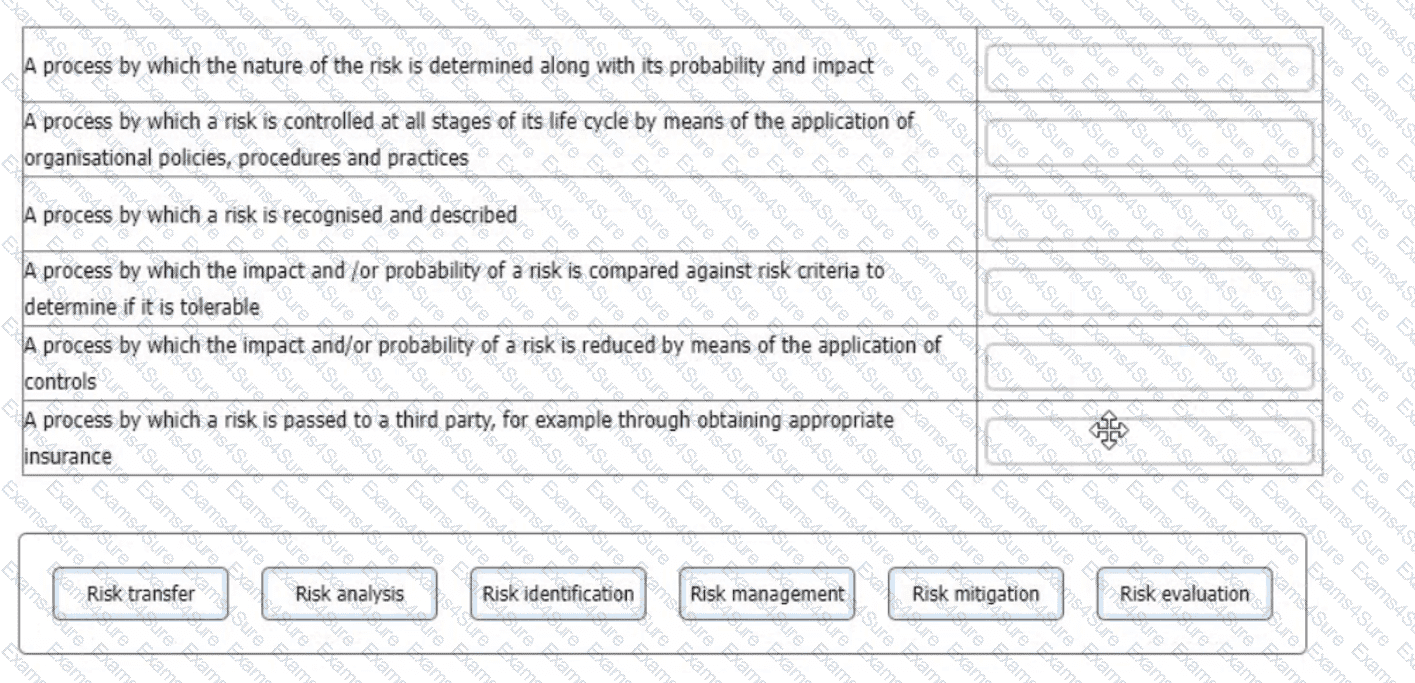
You are an experienced ISMS audit team leader providing instruction to an auditor in training. They are unclear in their understanding of risk processes and ask you to provide them with an example of each of the processes detailed below.
Match each of the descriptions provided to one of the following risk management processes.
To complete the table click on the blank section you want to complete so that it is highlighted in red, and then click on the applicable text from the options below. Alternatively, you may drag and drop each option to the appropriate blank section.
Scenario 8: EsBank provides banking and financial solutions to the Estonian banking sector since September 2010. The company has a network of 30 branches with over 100 ATMs across the country.
Operating in a highly regulated industry, EsBank must comply with many laws and regulations regarding the security and privacy of data. They need to manage information security across their operations by implementing technical and nontechnical controls. EsBank decided to implement an ISMS based on ISO/IEC 27001 because it provided better security, more risk control, and compliance with key requirements of laws and regulations.
Nine months after the successful implementation of the ISMS, EsBank decided to pursue certification of their ISMS by an independent certification body against ISO/IEC 27001 .The certification audit included all of EsBank’s systems, processes, and technologies.
The stage 1 and stage 2 audits were conducted jointly and several nonconformities were detected. The first nonconformity was related to EsBank’s labeling of information. The company had an information classification scheme but there was no information labeling procedure. As a result, documents requiring the same level of protection would be labeled differently (sometimes as confidential, other times sensitive).
Considering that all the documents were also stored electronically, the nonconformity also impacted media handling. The audit team used sampling and concluded that 50 of 200 removable media stored sensitive information mistakenly classified as confidential. According to the information classification scheme, confidential information is allowed to be stored in removable media, whereas storing sensitive information is strictly prohibited. This marked the other nonconformity.
They drafted the nonconformity report and discussed the audit conclusions with EsBank’s representatives, who agreed to submit an action plan for the detected nonconformities within two months.
EsBank accepted the audit team leader's proposed solution. They resolved the nonconformities by drafting a procedure for information labeling based on the classification scheme for both physical and electronic formats. The removable media procedure was also updated based on this procedure.
Two weeks after the audit completion, EsBank submitted a general action plan. There, they addressed the detected nonconformities and the corrective actions taken, but did not include any details on systems, controls, or operations impacted. The audit team evaluated the action plan and concluded that it would resolve the nonconformities. Yet, EsBank received an unfavorable recommendation for certification.
Based on the scenario above, answer the following question:
Which option justifies the unfavorable recommendation for certification? Refer to scenario 8.
You are an ISMS auditor conducting a third-party surveillance audit of a telecom's provider. You are in the equipment staging room where network switches are pre-programmed before being despatched to clients. You note that recently there has been a significant increase in the number of switches failing their initial configuration test and being returned for reprogramming.
You ask the Chief Tester why and she says, 'It's a result of the recent ISMS upgrade'. Before the upgrade each technician had their own hard copy work instructions. Now, the eight members of my team have to share two laptops to access the clients' configuration instructions online. These delays put pressure on the technicians, resulting in more mistakes being made'.
Based solely on the information above, which clause of ISO to raise a nonconformity against' Select one.
You are performing an ISO 27001 ISMS surveillance audit at a residential nursing home, ABC Healthcare Services. ABC uses a healthcare mobile app designed and maintained by a supplier, WeCare, to monitor residents' well-being. During the audit, you learn that 90% erf the residents' family members regularly receive medical device advertisements from WeCare, by email and SMS once a week. The service agreement between ABC and WeCare prohibits the supplier from using residents' personal data. ABC has received many complaints from residents and their family members.
The Service Manager says that the complaints were investigated as an information security incident which found that they were justified. Corrective actions have been planned and implemented according to the nonconformity and corrective action management procedure.
You write a nonconformity "ABC failed to comply with information security control
A.
5.34 (Privacy and protection of PII) relating to the personal data of residents' and their family members. A supplier, WeCare, used residents' personal information to send advertisements to family members"Select three options of the corrections and corrective actions listed that you would expect ABC to make in response to the nonconformity
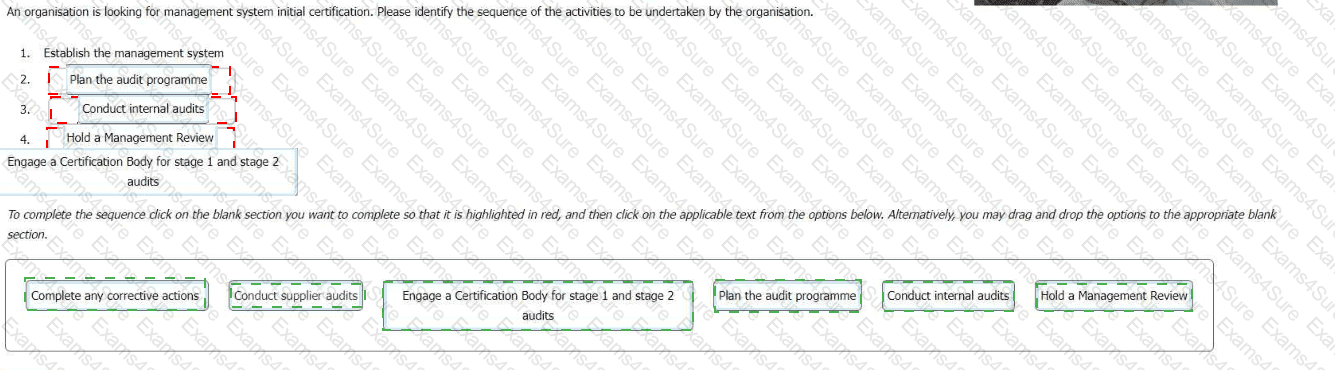
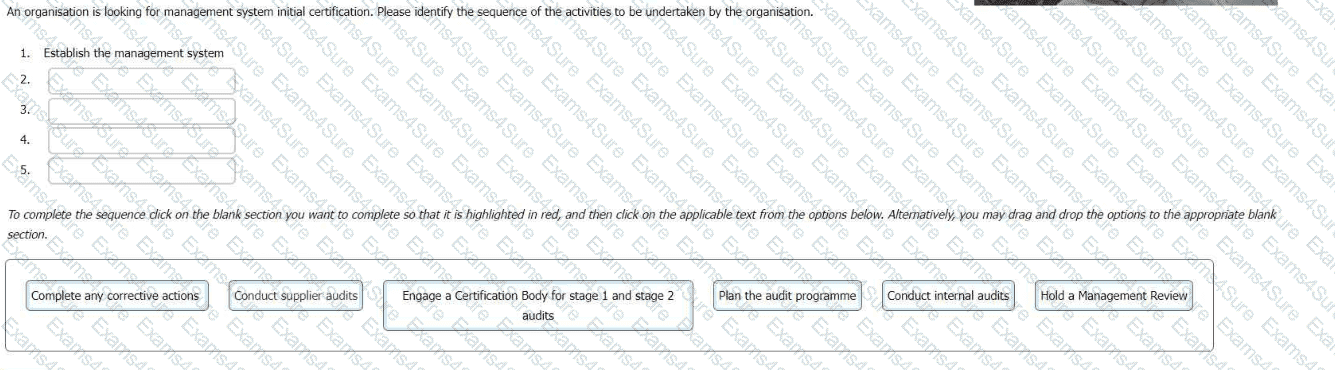
An organisation is looking for management system initial certification. Please identify the sequence of the activities to be undertaken by the organisation.
To complete the sequence click on the blank section you want to complete so that it is highlighted in red, and then click on the applicable text from the options below. Alternatively, you may drag and drop the options to the appropriate blank section.
Question:
An organization is evaluating the materiality of different processes within its ISMS. It is assessing the direct expenses involved with personnel, third-party services, and general fees. Which factor of materiality is the company primarily considering?
You are carrying out a third-party surveillance audit of a client's ISMS. You are currently in the secure storage area of the data centre where the organisation's customers are able to temporarily locate equipment coming into or going out of the site. The equipment is contained within locked cabinets and each cabinet is allocated to a single, specific client.
Out of the corner of your eye you spot movement near the external door of the storage area. This is followed by a loud noise. You ask the guide what is going on. They tell you that recent high rainfall has raised local river levels and caused an infestation of rats. The noise was a specialist pest control stunning device being triggered. You check the device in the corner and find there is a large immobile rat contained within it.
What three actions would be appropriate to take next?
You are an experienced ISMS audit team leader providing guidance to an ISMS auditor in training. They have been asked to carry out an assessment of external providers and have prepared a checklist containing the following activities. They have asked you to review their checklist to confirm that the actions they are proposing are appropriate.
The audit they have been invited to participate in is a third-party surveillance audit of a data centre . The data centre agent is part of a wider telecommunication group. Each data centre within the group operates its own ISMS and holds its own certificate.
Select three options that relate to ISO/IEC 27001:2022's requirements regarding external providers.
Scenario 3: Rebuildy is a construction company located in Bangkok.. Thailand, that specializes in designing, building, and maintaining residential buildings. To ensure the security of sensitive project data and client information, Rebuildy decided to implement an ISMS based on ISO/IEC 27001. This included a comprehensive understanding of information security risks, a defined continual improvement approach, and robust business solutions.
The ISMS implementation outcomes are presented below
•Information security is achieved by applying a set of security controls and establishing policies, processes, and procedures.
•Security controls are implemented based on risk assessment and aim to eliminate or reduce risks to an acceptable level.
•All processes ensure the continual improvement of the ISMS based on the plan-do-check-act (PDCA) model.
•The information security policy is part of a security manual drafted based on best security practices Therefore, it is not a stand-alone document.
•Information security roles and responsibilities have been clearly stated in every employees job description
•Management reviews of the ISMS are conducted at planned intervals.
Rebuildy applied for certification after two midterm management reviews and one annual internal audit Before the certification audit one of Rebuildy’s former employees approached one of the audit team members to tell them that Rebuildy has several security problems that the company is trying to conceal. The former employee presented the documented evidence to the audit team member Electra, a key client of Rebuildy, also submitted evidence on the same issues, and the auditor determined to retain this evidence instead of the former employee's. The audit team member remained in contact with Electra until the audit was completed, discussing the nonconformities found during the audit. Electra provided additional evidence to support these findings.
At the beginning of the audit, the audit team interviewed the company’s top management They discussed, among other things, the top management's commitment to the ISMS implementation. The evidence obtained from these discussions was documented in written confirmation, which was used to determine Rebuildy’s conformity to several clauses of ISO/IEC 27001
The documented evidence obtained from Electra was attached to the audit report, along with the nonconformities report. Among others, the following nonconformities were detected:
•An instance of improper user access control settings was detected within the company's financial reporting system.
•A stand-alone information security policy has not been established. Instead, the company uses a security manual drafted based on best security practices.
After receiving these documents from the audit team, the team leader met Rebuildy’s top management to present the audit findings. The audit team reported the findings related to the financial reporting system and the lack of a stand-alone information security policy. The top management expressed dissatisfaction with the findings and suggested that the audit team leader's conduct was unprofessional, implying they might request a replacement. Under pressure, the audit team leader decided to cooperate with top management to downplay the significance of the detected nonconformities. Consequently, the audit team leader adjusted the report to present a more favorable view, thus misrepresenting the true extent of Rebuildy's compliance issues.
Based on the scenario above, answer the following question:
Question:
Based on Scenario 3, the audit team used information obtained from interviews with top management to determine Rebuildy’s conformity to several ISO/IEC 27001 clauses. Is this acceptable?
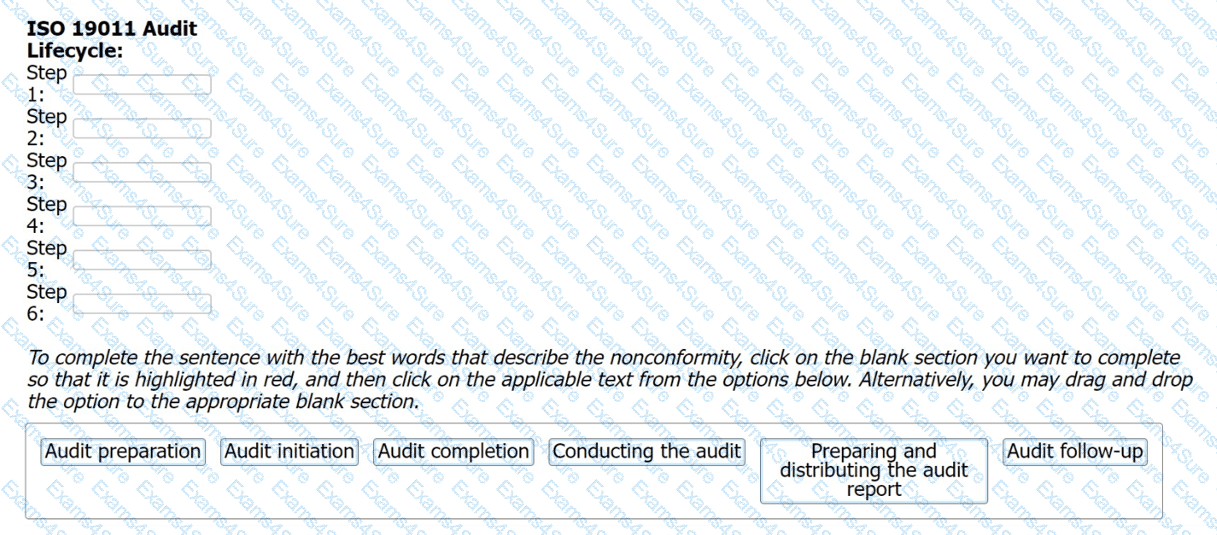
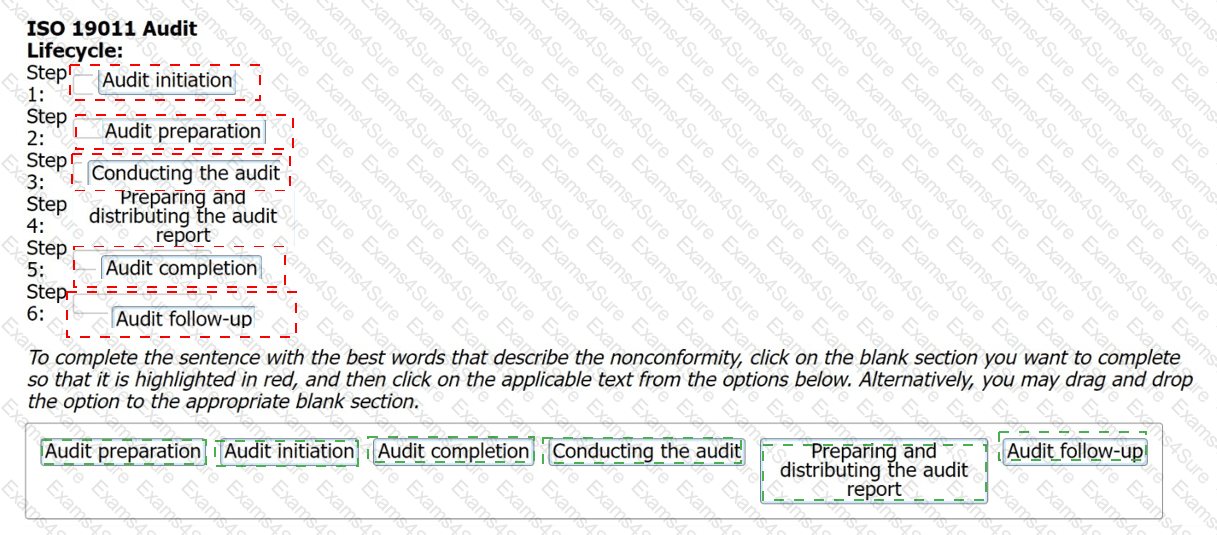
The audit lifecycle describes the ISO 19011 process for conducting an individual audit. Drag and drop the steps of the audit lifecycle into the correct sequence.