Huawei Certified ICT Professional - Constructing Service Security Network (HCIP-Security-CSSN V3.0)
Last Update 15 hours ago
Total Questions : 177
Huawei Certified ICT Professional - Constructing Service Security Network (HCIP-Security-CSSN V3.0) is stable now with all latest exam questions are added 15 hours ago. Incorporating H12-722 practice exam questions into your study plan is more than just a preparation strategy.
By familiarizing yourself with the Huawei Certified ICT Professional - Constructing Service Security Network (HCIP-Security-CSSN V3.0) exam format, identifying knowledge gaps, applying theoretical knowledge in Huawei practical scenarios, you are setting yourself up for success. H12-722 exam dumps provide a realistic preview, helping you to adapt your preparation strategy accordingly.
H12-722 exam questions often include scenarios and problem-solving exercises that mirror real-world challenges. Working through H12-722 dumps allows you to practice pacing yourself, ensuring that you can complete all Huawei Certified ICT Professional - Constructing Service Security Network (HCIP-Security-CSSN V3.0) exam questions within the allotted time frame without sacrificing accuracy.
USG6000V software logic architecture is divided into three planes: management plane, control plane and
Regarding the description of intrusion detection technology, which of the following statements is correct?
Which of the following options belong to the upgrade method of the anti-virus signature database of Huawei USG6000 products? (multiple choice)
With regard to APT attacks, the attacker often lurks for a long time and launches a formal attack on the enterprise at the key point of the incident.
Generally, APT attacks can be summarized into four stages:
1. Collecting Information & Intrusion
2. Long-term lurking & mining
3. Data breach
4. Remote control and penetration
Regarding the order of these four stages, which of the following options is correct?
Analysis is the core function of intrusion detection. The analysis and processing process of intrusion detection can be divided into three phases; build an analyzer to perform analysis on actual field data.
Which of the analysis, feedback and refinement is the function included in the first two stages?
If the processing strategy for SMTP virus files is set to alert, which of the following options is correct?
An enterprise administrator configures a Web reputation website in the form of a domain name, and configures the domain name as www. abc; example. com. .
Which of the following is the entry that the firewall will match when looking up the website URL?
The user needs of a university are as follows:
1. The environment is large, and the total number of two-way traffic can reach 800M. Huawei USG6000 series firewall is deployed at its network node.
2. The intranet is divided into student area, server area, etc., users are most concerned about the security of the server area to avoid attacks from various threats.
3. At the same time, some pornographic websites in the student area are prohibited.
The external network has been configured as an untrust zone and the internal network has been configured as a trust zone on the firewall. How to configure the firewall to meet the above requirements?
155955cc-666171a2-20fac832-0c042c0415
Regarding the anti-spam response code, which of the following statements is wrong?
In the penetration stage of an APT attack, which of the following attack behaviors will the attacker generally have?
The results of the RBL black and white list query on the firewall are as follows:
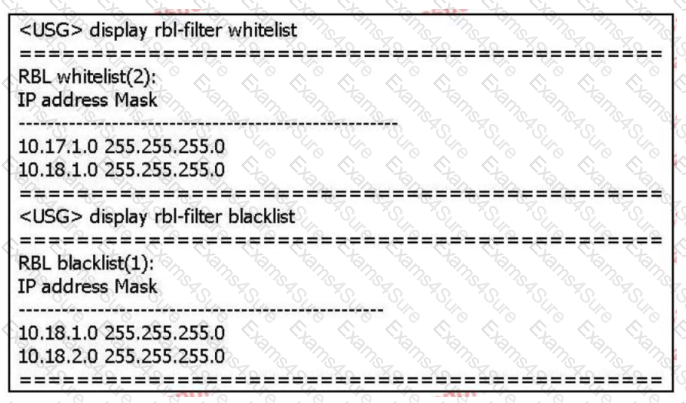
Based on the above information only, which of the following statements is correct? (multiple choice)
The processing flow of IPS has the following steps;
1. Reorganize application data
2. Match the signature
3. Message processing
4. Protocol identification
Which of the following is the correct order of the processing flow?
Which of the following attacks are attacks against web servers? (multiple choices)
Huawei's USG000 product can identify the true type of common files and over-check the content. Even if the file is hidden in a compressed file, or change the extension
The name of the exhibition can't escape the fiery eyes of the firewall.
In the following options, which of the two attacks use similar attack methods, they will generate a large number of useless response packets, occupying network bandwidth,
Consume equipment resources?
Intrusion detection is a network security technology used to detect any damage or attempt to damage the confidentiality, integrity or availability of the system. Which of the following
What is the content of the intrusion detection knowledge base?
In the big data intelligent security analysis platform, it is necessary to collect data from data sources, and then complete a series of actions such as data processing, detection and analysis, etc.
do. Which of the following options does not belong to the action that needs to be completed in the data processing part?
155955cc-666171a2-20fac832-0c042c0422
In the Huawei USG6000 product, after creating or modifying the security configuration file, the configuration content will not take effect immediately: you need to click the "Prompt" in the upper right corner of the interface.
"Hand in" to activate.
For Huawei USG600 products, which of the following statements about mail filtering configuration is correct?
Configure the following commands on the Huawei firewall:
[USG] interface G0/0/1
[USG] ip urpf loose allow-defult-route acl 3000
Which of the following options are correct? (multiple choice)
The most common form of child-like attack is to send a large number of seemingly legitimate packets to the target host through Flood, which ultimately leads to network bandwidth.
Or the equipment resources are exhausted. Which of the following options is not included in traffic attack packets?
Regarding the file filtering technology in the USG6000 product, which of the following options is wrong?
When using the two-way SSL function to decrypt HTTPS packets, the value of the reverse proxy level represents the number of times the packet can be decrypted.


TESTED 07 May 2024
Hi this is Romona Kearns from Holland and I would like to tell you that I passed my exam with the use of exams4sure dumps. I got same questions in my exam that I prepared from your test engine software. I will recommend your site to all my friends for sure.
Our all material is important and it will be handy for you. If you have short time for exam so, we are sure with the use of it you will pass it easily with good marks. If you will not pass so, you could feel free to claim your refund. We will give 100% money back guarantee if our customers will not satisfy with our products.