200-201 Practice Questions
Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Last Update 1 day ago
Total Questions : 476
Dive into our fully updated and stable 200-201 practice test platform, featuring all the latest CyberOps Associate exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CyberOps Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-201. Use this test to pinpoint which areas you need to focus your study on.
Refer to the exhibit.
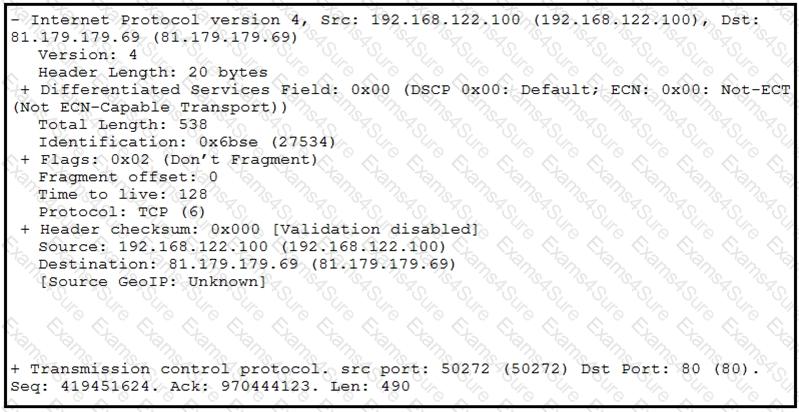
What should be interpreted from this packet capture?
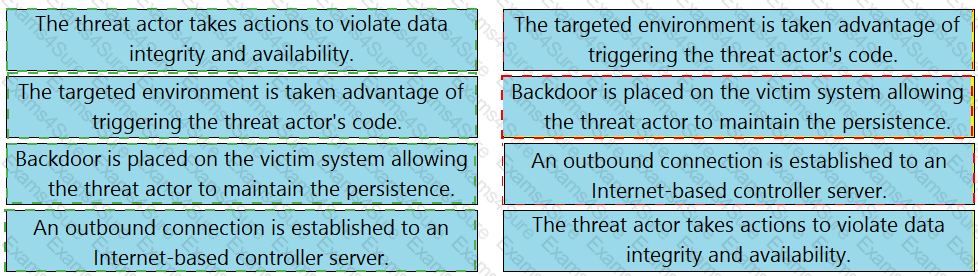
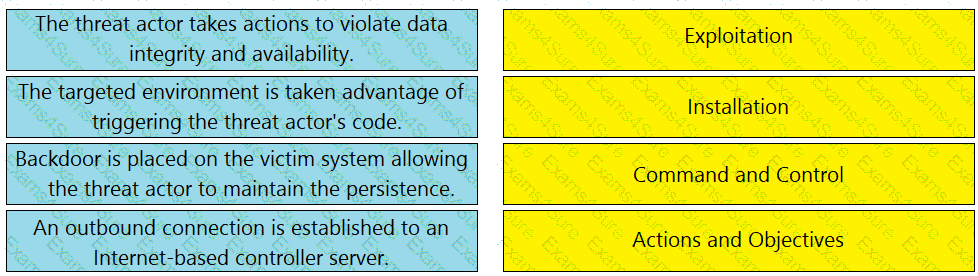
Drag and drop the definition from the left onto the phase on the right to classify intrusion events according to the Cyber Kill Chain model.
A company receptionist received a threatening call referencing stealing assets and did not take any action assuming it was a social engineering attempt. Within 48 hours, multiple assets were breached, affecting the confidentiality of sensitive information. What is the threat actor in this incident?
Why should an engineer use a full packet capture to investigate a security breach?
A security engineer must implement an Intrusion Prevention System (IPS) inside an organization’s DMZ. One of the requirements is the ability to block suspicious traffic in real time based on a triggered signature. The IPS will be connected behind the DMZ firewalls directly to the core switches. Which traffic integration method must be implemented to complete this project?
What are two differences between tampered disk images and untampered disk images'? (Choose two.)
Which type of attack uses a botnet to reflect requests off of an NTP server to overwhelm a target?
Which metric in CVSS indicates an attack that takes a destination bank account number and replaces it with a different bank account number?