200-201 Practice Questions
Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Last Update 1 day ago
Total Questions : 476
Dive into our fully updated and stable 200-201 practice test platform, featuring all the latest CyberOps Associate exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CyberOps Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-201. Use this test to pinpoint which areas you need to focus your study on.
Which security technology guarantees the integrity and authenticity of all messages transferred to and from a web application?
An employee reports that someone has logged into their system and made unapproved changes, files are out of order, and several documents have been placed in the recycle bin. The security specialist reviewed the system logs, found nothing suspicious, and was not able to determine what occurred. The software is up to date; there are no alerts from antivirus and no failed login attempts. What is causing the lack of data visibility needed to detect the attack?
A compliance analyst receives a complaint from a customer regarding personal data being unlawfully retained despite a deletion request. The company is based in Europe and must comply with GDPR. The only data collected is the email address 0524l9i75@gmail.com. How should the compliance analyst act?
An engineer is investigating a case of the unauthorized usage of the “Tcpdump” tool. The analysis revealed that a malicious insider attempted to sniff traffic on a specific interface. What type of information did the malicious insider attempt to obtain?
According to the September 2020 threat intelligence feeds a new malware called Egregor was introduced and used in many attacks. Distnbution of Egregor is pnmanly through a Cobalt Strike that has been installed on victim's workstations using RDP exploits Malware exfiltrates the victim's data to a command and control server. The data is used to force victims pay or lose it by publicly releasing it. Which type of attack is described?
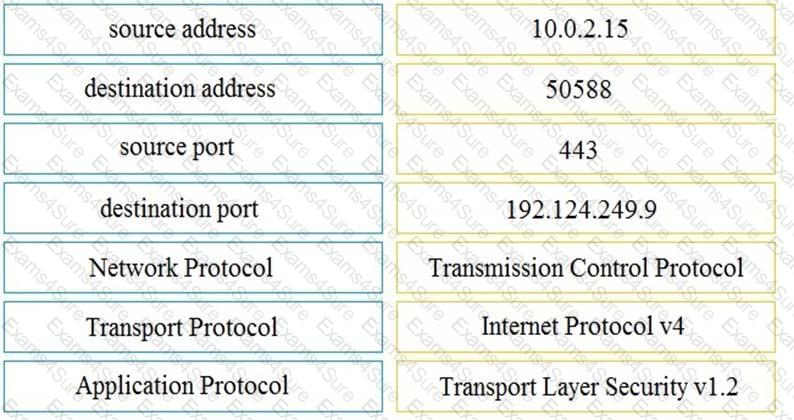
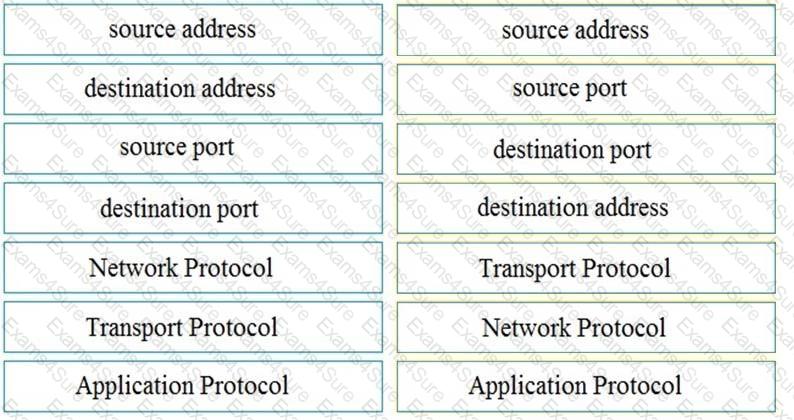
Refer to the exhibit.
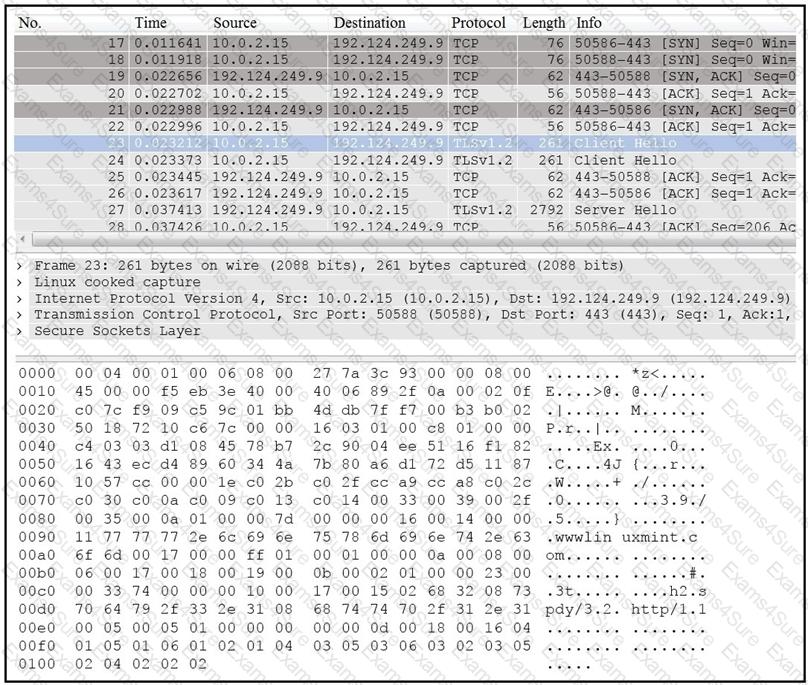
Drag and drop the element name from the left onto the correct piece of the PCAP file on the right.