
200-201 Practice Questions
Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Last Update 1 day ago
Total Questions : 476
Dive into our fully updated and stable 200-201 practice test platform, featuring all the latest CyberOps Associate exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CyberOps Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-201. Use this test to pinpoint which areas you need to focus your study on.
What is the impact of false positive alerts on business compared to true positive?
An analyst received a ticket regarding a degraded processing capability for one of the HR department's servers. On the same day, an engineer noticed a disabled antivirus software and was not able to determine when or why it occurred. According to the NIST Incident Handling Guide, what is the next phase of this investigation?
What is the difference between statistical detection and rule-based detection models?
Which principle is being followed when an analyst gathers information relevant to a security incident to determine the appropriate course of action?
Refer to the exhibit.
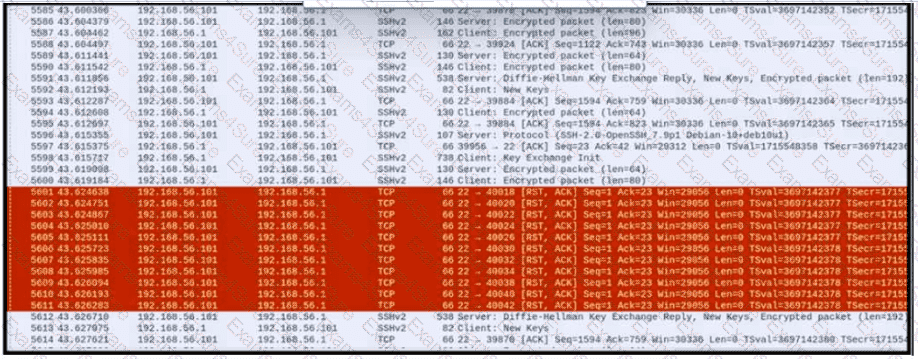
An engineer is analyzing a PCAP file after a recent breach An engineer identified that the attacker used an aggressive ARP scan to scan the hosts and found web and SSH servers. Further analysis showed several SSH Server Banner and Key Exchange Initiations. The engineer cannot see the exact data being transmitted over an encrypted channel and cannot identify how the attacker gained access How did the attacker gain access?
An employee of a company receives an email with an attachment. They notice that this email is from a suspicious source, and they decide not to open the attached file. After further investigation, a security analyst concludes that this file is malware. To which category of the Cyber Kill Chain model does this event belong?
Which technology on a host is used to isolate a running application from other applications?



