200-201 Practice Questions
Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Last Update 1 day ago
Total Questions : 476
Dive into our fully updated and stable 200-201 practice test platform, featuring all the latest CyberOps Associate exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CyberOps Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-201. Use this test to pinpoint which areas you need to focus your study on.
An analyst received an alert on their desktop computer showing that an attack was successful on the host. After investigating, the analyst discovered that no mitigation action occurred during the attack. What is the reason for this discrepancy?
Which open-sourced packet capture tool uses Linux and Mac OS X operating systems?
What is the advantage of agent-based protection compared to agentless protection?
What is the difference between deep packet inspection and stateful inspection?
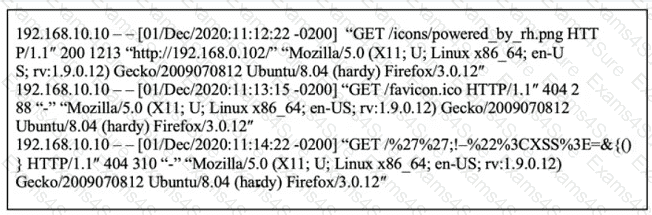
Refer to the exhibit.
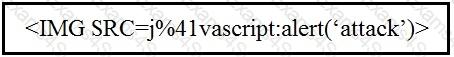
Which kind of attack method is depicted in this string?
What are two differences in how tampered and untampered disk images affect a security incident? (Choose two.)
An organization that develops high-end technology is going through an internal audit The organization uses two databases The main database stores patent information and a secondary database stores employee names and contact information A compliance team is asked to analyze the infrastructure and identify protected data Which two types of protected data should be identified? (Choose two)
STION NO: 102
Refer to the exhibit.
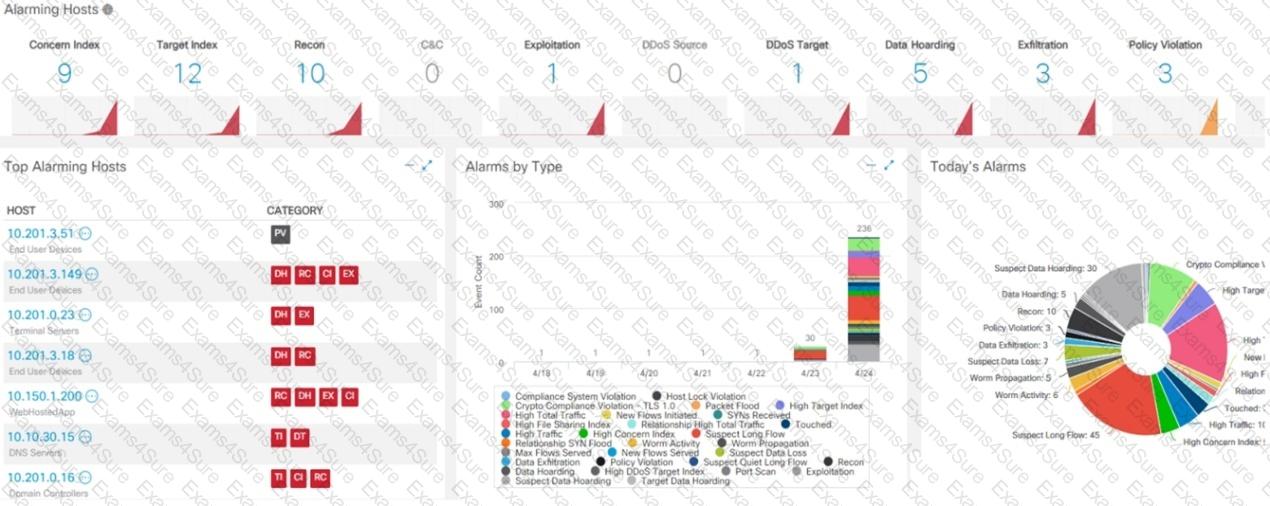
What is the potential threat identified in this Stealthwatch dashboard?