
200-201 Practice Questions
Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Last Update 1 day ago
Total Questions : 476
Dive into our fully updated and stable 200-201 practice test platform, featuring all the latest CyberOps Associate exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CyberOps Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-201. Use this test to pinpoint which areas you need to focus your study on.
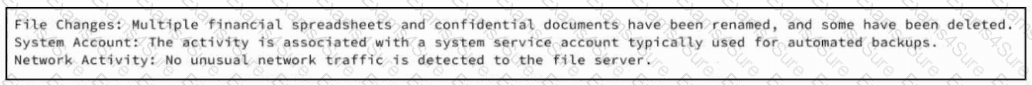
Refer to the exhibit. A SOC team member receives a case from his colleague with notes attached. The artifacts and alerts associated with the case must be analyzed and a conclusion must be provided. What is the cause of the alert?
How does the approach of a behavioral detection system to identifying security threats compare to that of a rule-based detection system?
Refer to the exhibit.
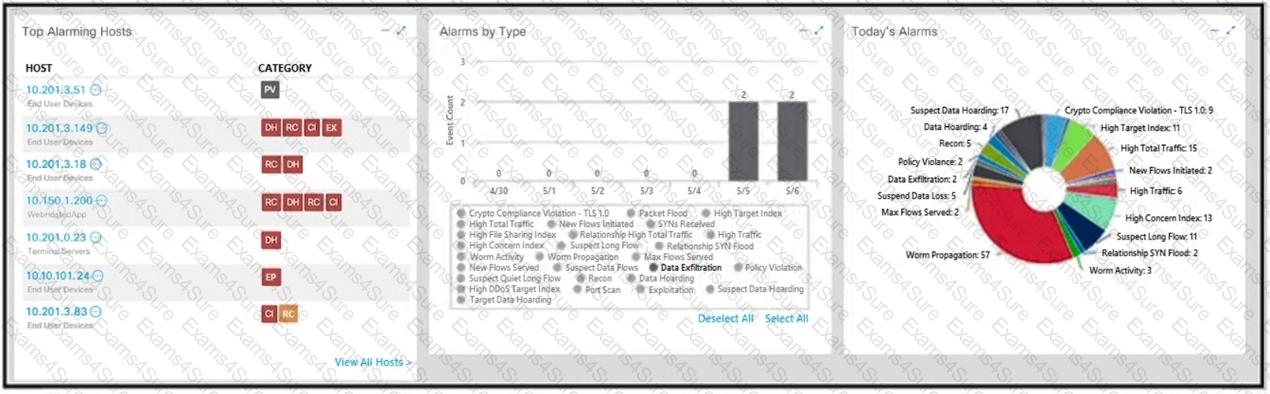
What is the potential threat identified in this Stealthwatch dashboard?
What describes the impact of false-positive alerts compared to false-negative alerts?
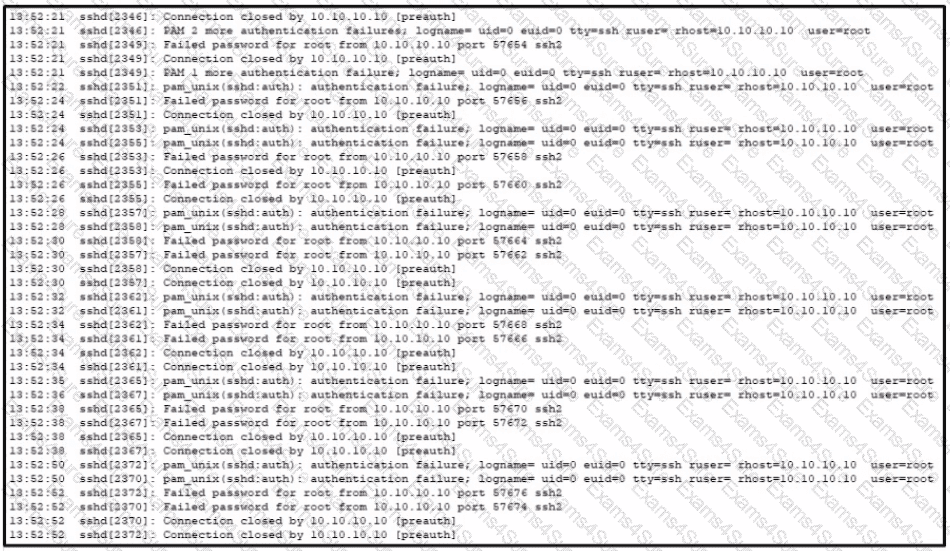
Refer to the exhibit A SOC analyst is examining the Auth.log file logs of one the breached systems What is the possible reason for this event log?
According to the NIST SP 800-86. which two types of data are considered volatile? (Choose two.)
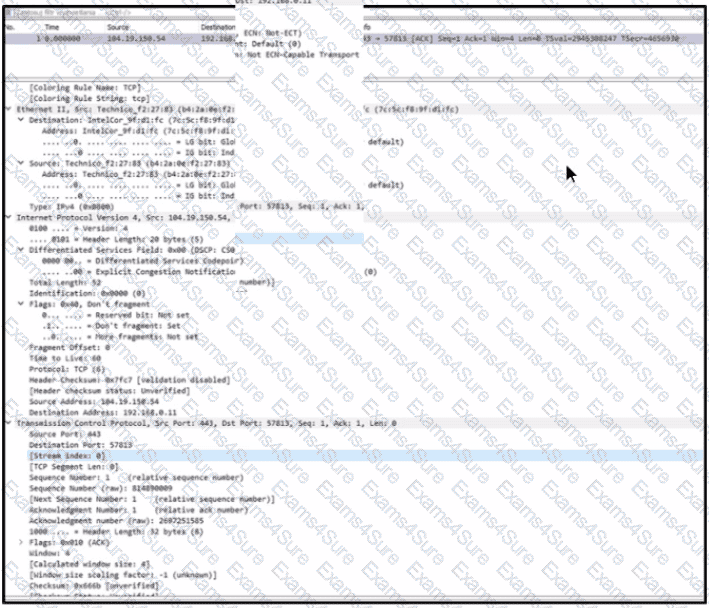
Refer to the exhibit.
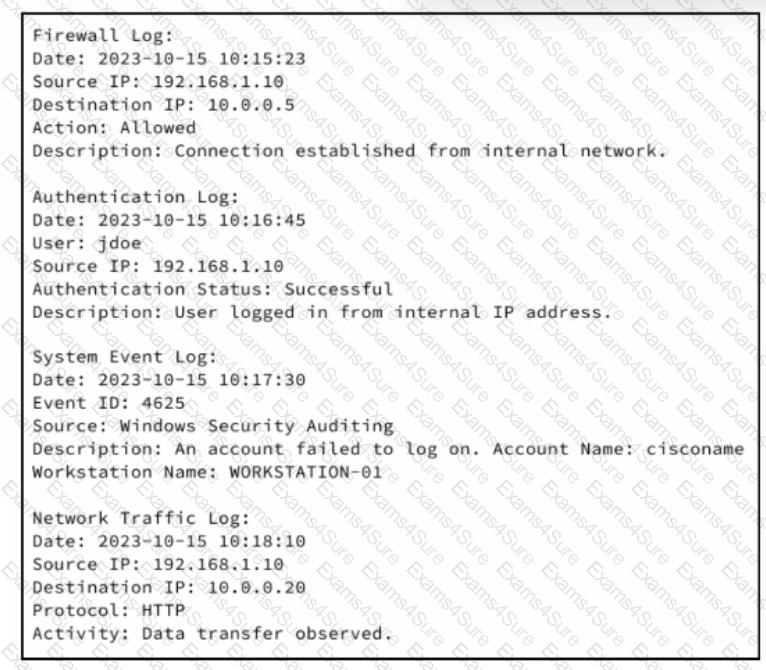
An analyst receives an IDS alert pertaining to a possible data exfiltration attempt. An additional set of logs is collected from different systems and analyzed. Which type of evidence do the logs provide in relation to the primary alert from the IDS?
Refer to the exhibit.
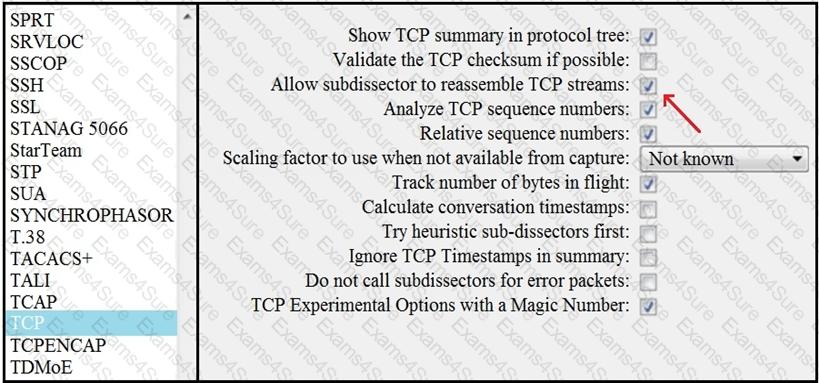
What is the expected result when the "Allow subdissector to reassemble TCP streams" feature is enabled?
Refer to the exhibit. An engineer must use a 5-tuple approach to isolate a compromised host in a grouped set of logs.
Which data must the engineer use?



