
200-201 Practice Questions
Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Last Update 1 day ago
Total Questions : 476
Dive into our fully updated and stable 200-201 practice test platform, featuring all the latest CyberOps Associate exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CyberOps Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-201. Use this test to pinpoint which areas you need to focus your study on.
Which security monitoring data type is associated with application server logs?
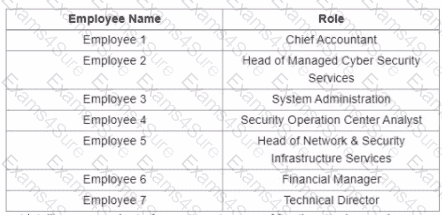
Refer to the exhibit.
A suspicious IP address is tagged by Threat Intelligence as a brute-force attempt source After the attacker produces many of failed login entries, it successfully compromises the account. Which stakeholder is responsible for the incident response detection step?
An engineer must gather data for monitoring purposes from different network devices. The engineer needs to collect events from the local network and use that information for packet sniffing. The solution must create an exact copy of traffic and provide full fidelity. Which solution should the engineer use?
Which step in the incident response process researches an attacking host through logs in a SIEM?



