
200-201 Practice Questions
Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
Last Update 1 day ago
Total Questions : 476
Dive into our fully updated and stable 200-201 practice test platform, featuring all the latest CyberOps Associate exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CyberOps Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-201. Use this test to pinpoint which areas you need to focus your study on.
What should an engineer use to aid the trusted exchange of public keys between user tom0411976943 and dan1968754032?
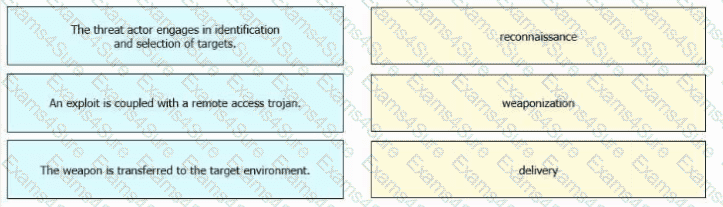
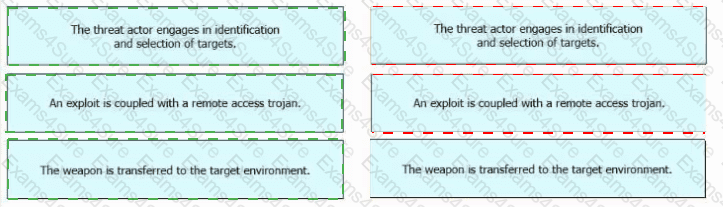
Drag and drop the definitions from the left onto the phases on the right to classify intrusion events according to the Cyber Kill Chain model.
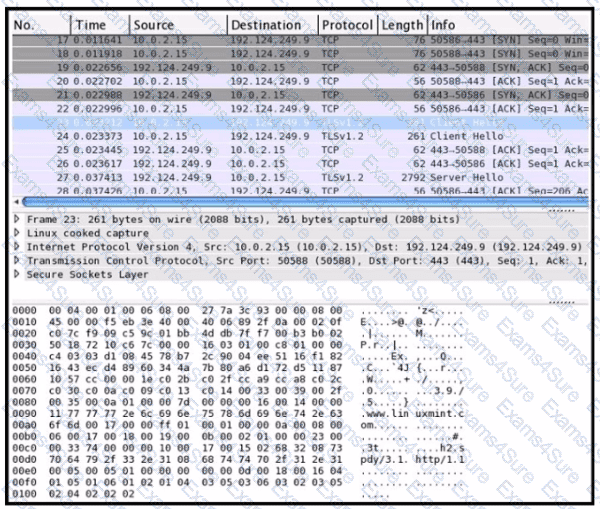
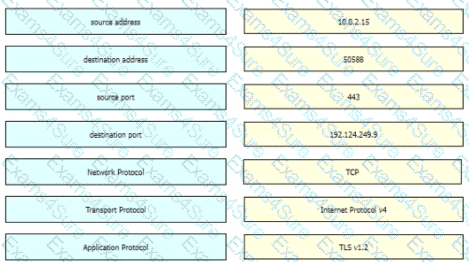
Refer to the exhibit Drag and drop the element names from the left onto the corresponding pieces of the PCAP file on the right.
Which attack is the network vulnerable to when a stream cipher like RC4 is used twice with the same key?
Which access control should a chief information security officer select to protect extremely sensitive data categorized at various levels of confidentiality?
What are the two differences between stateful and deep packet inspection? (Choose two )
What is a benefit of agent-based protection when compared to agentless protection?
An organization's security team detected network spikes coming from the internal network. An investigation concluded that the spike in traffic was from intensive network scanning. How must the analyst collect the traffic to isolate the suspicious host?



 A screenshot of a computer Description automatically generated
A screenshot of a computer Description automatically generated
